Initial Access Brokers Leverage Legitimate Google Ads to Gain Malicious Access

A threat actor tracked as DEV-0569 appears to be using a combination of Google Ads and impersonated websites to compromise credentials and distribute malware to gain network access.
These days there is plenty of talk about Initial Access Brokers, but often, little is known about their specific actions other than the resulting presence of access to networks and assumptions that they are using the same tactics and techniques as cybercriminals that are responsible for an entire attack.
Recent Twitter posts from cybersecurity researchers like Germán Fernández, DEV-0569 is using Google ads to infect victim machines.
1/ DEV-0569, current distribution via #GoogleAds.
1.- #Gozi aka #Ursnif (bot) ↓
2.- #RedLine (stealer) ↓
And if the conditions are right, possibly:
3.- #CobaltStrike (C2) ↓
4.- #Royal Ransomware 💥
(No more BatLoader in the infection chain) pic.twitter.com/mYp8hSU7FH— Germán Fernández (@1ZRR4H) January 21, 2023
According to Bleeping Computer, the ads are for software titles including LightShot, Rufus, 7-Zip, FileZilla, LibreOffice, AnyDesk, Awesome Miner, TradingView, WinRAR, and VLC.
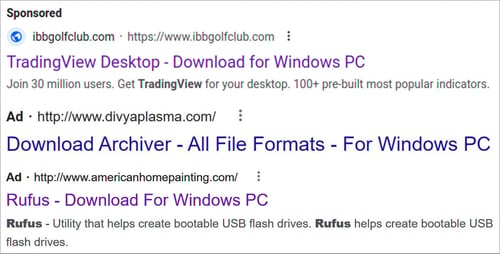
Source: Bleeping Computer
This ad takes victims to a lookalike website where the desired tool (read: malware) can be downloaded and installed. In the end, a foothold is established by DEV-0569 on an endpoint within a victim organization, with its access sold on the dark web.
The use of ads is a smart use of social engineering. When’s the last time you assumed a Google ad was not only illegitimate, but malicious? Right… never.
This kind of simple innovation is why organizations – including and especially members of IT – need to undergo continual Security Awareness Training that keeps them up to date on the latest social engineering tactics and phishing scams. The alternative is, eventually, one of these malicious methods is going to fool just the right person within your organization.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
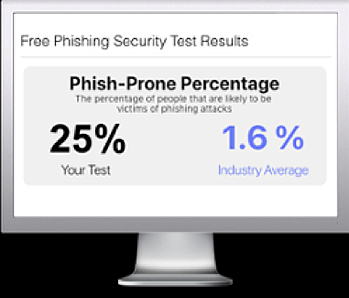
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

