MetaMask Crypto Wallet Phishing

A phishing campaign attempting to steal credentials for MetaMask cryptocurrency wallets, according to Lauryn Cash at Armorblox.
“The socially engineered email was titled ‘Re: [Request Updated] Ticket: 6093-57089-857’ and looked to be sent from MetaMask support email: support@metamask.as,” Cash writes. “The email body spoofed a Know Your Customer (KYC) verification request and claimed that not complying with KYC regulations would result in restricted access to MetaMask wallet. The email prompted the victim to click the ‘Verify your Wallet’ button to complete the wallet verification.”
The link in the email leads to a spoofed MetaMask login page.
“Upon clicking the ‘Verify your Wallet’ button, within the email, the victim was redirected to a fake landing page – one that closely resembled a legitimate MetaMask verification page,” Cash says. “The victim was prompted to enter his or her Passphrase in order to comply with KYC regulations and to continue the use of MetaMask service. Attackers utilized MetaMask branding, logo, and referenced Passphrase credentials – of which all are associated with the legitimate MetaMask brand. This look-a-like page could easily fool unsuspecting victims, especially those who do not realize that MetaMask does not ask users to comply with KYC regulations.”
The phishing page also contained security advice in order to lend legitimacy to the scam.
“The language on the fake landing page even reminded victims to make sure his or her passphrase is always protected and to double-check that nobody is watching,” Cash writes. “It’s language like this that can evoke trust, one of the primary goals of the attacks. If victims fell for this attack, they would have entered their passphrase credentials, sensitive information that attacks were aiming to exfiltrate through this email attack…. The context of this attack also leverages the curiosity effect, which is a cognitive bias that refers to our innate desire to resolve uncertainty and know more about something.”
New-school security awareness training can enable your employees to recognize phishing attacks.
Armorblox has the story.
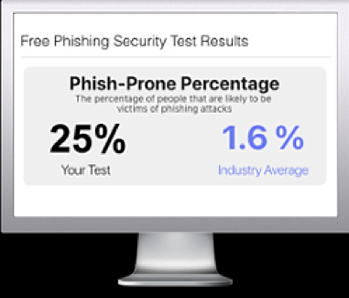
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

