Phishing Campaign Impersonates Shipping Giant Maersk

Researchers at Vade Secure warn of a large phishing campaign that’s impersonating shipping giant Maersk to target thousands of users.
“Several waves of phishing emails impersonating Maersk have targeted more than 18,000 recipients, 13,000 recipients, and 5,000 recipients respectively between January 2022 and May 2022, exploiting the global supply chain crisis affecting millions of businesses around the world,” the researchers write. “Users in New Zealand have been targeted with Maersk phishing emails with the subject line ‘Maersk Original Shipping Document’ followed by the email of the recipient and the from address displayed as service@maersk[.]com, which mimics a legitimate Maersk email address.”
The emails contain a link to a spoofed login page that asks the user to enter their email address and password in order to access their shipping information. The attackers are using compromised websites to host these phishing pages.
“Maersk phishing campaigns have been active since 2018, but this most recent campaign spiked in March and April 2022,” the researchers write. “Previous research suggests a link between the 2018 Maersk campaign and the ‘MartyMcFly’ investigation into attacks targeting the Italian naval industry. Like the previous campaign, the current campaign is using compromised websites to host phishing kits and potentially malware.”
The researchers add that New Zealand is a prime target for shipping-themed phishing attacks due to its location, particularly during the pandemic.
“New Zealand has been hit hard by the supply chain crisis, with products sitting in warehouses and no ships to transport them,” Vade says. “New Zealand’s size and geographical location makes it particularly vulnerable, with shipping companies prioritizing business with larger and more accessible countries. This makes anxious New Zealand businesses optimal targets for phishing attacks.”
New-school security awareness training can give your organization an essential layer of defense by teaching your employees how to thwart social engineering attacks.
Will your users respond to phishing emails?
KnowBe4’s Phishing Reply Test (PRT) is a complimentary IT security tool that makes it easy for you to check to see if key users in your organization will reply to a highly targeted phishing attack without clicking on a link. PRT will give you quick insights into how many users will take the bait so you can take action to train your users and better protect your organization from these fraudulent attacks!
Here’s how it works:
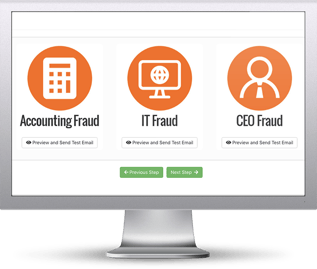
- Immediately start your test with your choice of three phishing email reply scenarios
- Spoof a Sender’s name and email address your users know and trust
- Phishes for user replies and returns the results to you within minutes
- Get a PDF emailed to you within 24 hours with the percentage of users that replied
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-reply-test-partner?partnerid=001a000001lWEoJAAW

