Ransomware Gangs Improve Attack Speed and Evade Detection with New “Intermittent Encryption” Tactic

As ransomware gangs look for new ways to improve their execution, this relatively new encryption tactic has been gaining popularity in multiple ransomware families.
If you were a developer of ransomware software, what would your two biggest improvement goals be for your software that help achieve greater success in receiving a ransom payment? I’d guess avoiding detection and a faster encryption speed – all to ensure the maximum amount of data is encrypted before any incident response efforts can take place.
According to the security researchers at Sentinel Labs, a tactic first seen in mid-2021 has been growing in adoption among ransomware gangs. Called Intermittent Encryption, this tactic only encrypts a portion of a file, but just enough to render it useless. There are three modes seen in the wild:
- Skip-Step – this “steps” through and encrypts a certain number of MBs, and then “skips” another number of MBs
- Percent – like Skip-Step, but skipping a percent of the file, rather than a specific number of MBs
- Fast – Encrypts the first X MBs of a file
A number of ransomware families have recently adopted this method, including Qyick, Agenda, BlackCat, PLAY, and Black Basta.
The benefit of using such an encryption method is that it helps achieve the two goals previously mentioned: because it only encrypts a portion of the file, more data can be encrypted in the same amount of time. And because the process is less disk-intensive, it’s less likely to trigger alerts based on disk usage.
The warning here is that, as this method proves to be successful in encrypting more of an environment, more ransomware families will adopt it, making ransomware even more dangerous and it more necessary for organizations to utilize Security Awareness Training to educate users on how to spot social engineering in both web- and email-based attacks attempting to gain entrance into the organization’s network.
Free Ransomware Simulator Tool
Threat actors are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 22 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
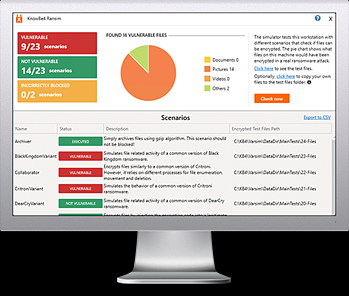
Here’s how it works:
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 23 types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/ransomware-simulator-tool-partner?partnerid=001a000001lWEoJAAW

