Remote workers routinely bypassed security tools during pandemic
More than a quarter of security leaders in the UK say remote-working employees either circumvented or purposely turned off security tools and services, and a third admit compromising their organisation’s security to some degree in order to facilitate the practice, according to newly published data from Palo Alto Networks.
The firm’s latest report, The state of hybrid workforce security 2021, includes input from 3,000 information security, network operations and application development professionals around the world in an attempt to understand how the shift to remote work impacted network security infrastructure, and how the past 18-20 months have affected network security strategies as regards protecting home workers.
Of the UK-based respondents, 35% tended to agree that remote security measures had introduced “significant productivity challenges” for remote employees, and 16% strongly agreed with this statement. As a result, 31% said employees were ignoring security measures, and 28% said they were disabling or circumventing them in some way.
UK IT leaders also tended to agree that remote security measures introduced significant management costs and/or overheads – 56% in total, and 49% said remote security measures were introducing more complexity. A total of 22% also said their network could no longer support remote working demand.
Palo Alto said it was important to recognise that most organisations were fully aware of the nature of the cyber risk they were taking on during the transition to remote working, and many found themselves in a tricky situation where it was difficult or impossible to procure the needed technology. Unfortunately, the report said, those that found themselves in this position have subsequently borne negative consequences, from policy violations such as unsanctioned app usage or acceptable use violations, through to full-blown cyber attacks.
“As network and security professionals, we know we are always in a high stakes game of whack-a-mole,” wrote Jason Georgi, Palo Alto’s field CTO for its Prisma Access and SASE products, in the report’s preamble. “Just when we knock one issue down (like completely rearchitecting networks for remote access rather than onsite connectivity), new challenges arise. Based on what we heard in this survey, maintaining comprehensive network security is now your key challenge.
“If we look at this challenge more closely, 51% of survey respondents stated they have difficulty maintaining comprehensive network security. Perhaps what is even more concerning is that 61% of respondents noted they struggle to provide the necessary remote security to support work-from-home capabilities.
“At the beginning of the pandemic, most organisations’ immediate concern was how to stay running and keep people working, even if they couldn’t return physically to the workplace. Based on what we learned in the survey, this immediate shift to remote work turned network access and network security into equally high, yet competing, priorities for network and security professionals. Ultimately, network access emerged the winner.”
So, we have an interesting juncture; IT leaders know less than secure users and devices are planning on coming back to the office. So, what are they to do? The device issue is easy enough to fix; only managed devices should be used (keeping in mind there are solutions that exist that can manage and secure personal devices out there). The employee issue is going to require Security Awareness Training to both educate users on why being vigilant is important, what good cybersecurity hygiene looks like, and how to identify social engineering attacks via email and the web.
With thanks to Computer Weekly. The full story is here: https://www.computerweekly.com/news/252506084/Remote-workers-routinely-bypassed-security-tools-during-pandemic
The world’s largest library of security awareness training content is now just a click away!
In your fight against phishing and social engineering you can now deploy the best-in-class simulated phishing platform combined with the world’s largest library of security awareness training content; including 1000+ interactive modules, videos, games, posters and newsletters.
You can now get access to our new ModStore Preview Portal to see our full library of security awareness content; you can browse, search by title, category, language or content topics.
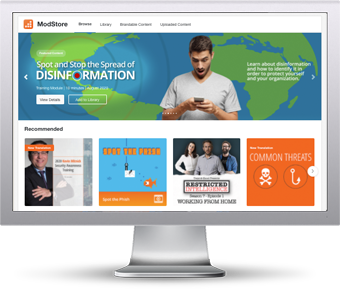
The ModStore Preview includes:
- Interactive training modules
- Videos
- Trivia Games
- Posters and Artwork
- Newsletters and more!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/security-awareness-training-preview-partner?partnerid=001a000001lWEoJAAW


