When It Comes to Password Hygiene, Users Say One Thing, But Do Another

With credentials being at the forefront of most cyberattacks, the need for strong, unique passwords is at an all-time high. But new data shows users know what to do, but don’t do it.
We’ve seen how the majority of phishing attacks target credentials, so it becomes increasingly important for those stolen credentials to only provide access to a singular platform/application/etc. But, that only works IF (and it’s a pretty big if!) users utilize unique usernames and passwords for each and every system.
According to LastPass’ Psychology of Passwords report, users are a bit apathetic to the cause of securing the organization with proper password hygiene:
- 51% of users rely on their memory to keep track of passwords, despite 79% agreeing that compromised passwords are concerning
- 65% always or mostly still use the same password or a variation, despite 92% admitting that they know using the same password or a variation is a risk
Now add in working remotely – something I’ve written about a number of times as not helping the organization’s security stance – and LastPass shows users aren’t looking out for their organization:
- 47% have not changed their online security habits since working remotely
- 46% have not strengthened their passwords while working remotely
- 44% have shared sensitive information and passwords for professional accounts while working remotely
In short, users are not concerned (or are made to be concerned) with password security. Security Awareness Training assists with not just educating users on scams, phishing attacks, social engineering tactics, and the like, but also teaches users why they need to be vigilant, use good password hygiene, and participate in the organization security.
This password problem can only be addressed through educating the user; Security Awareness Training is the key.
Are your user’s passwords…P@ssw0rd?
Employees are the weakest link in network security, using weak passwords and falling for phishing and social engineering attacks. KnowBe4’s complimentary Weak Password Test (WPT) checks your Active Directory for several different types of weak password related threats.
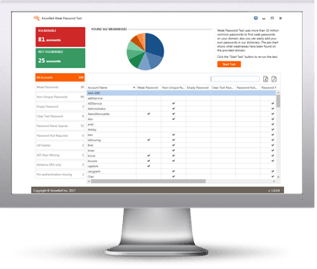
Here’s how it works:
- Reports on the accounts that are affected
- Tests against 10 types of weak password related threats
- Does not show/report on the actual passwords of accounts
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/weak-password-test-partner?partnerid=001a000001lWEoJAAW

