Criminals Use Search Engine Poisoning to Boost Phishing Pages

Researchers at Malwarebytes warn that cybercriminals are using search engine poisoning to boost phishing pages to the top of Bing’s search results.
The researchers found when they searched “KeyBank login” in Bing, a spoofed KeyBank login page appeared above KeyBank’s official site.
“The domain name used is ixx-kexxx[.]com which was registered on November 15,” the researchers write. “Given that it is only two weeks old and yet came up before ibx.key.com (the real website), we surmise that the attackers are abusing Bing’s search algorithms.”
After clicking the link, users will be redirected to a convincingly spoofed version of KeyBank’s site, where they’ll be asked to enter their username and password. If the user complies, the site will show a “slow connectivity” message while the crooks enter the stolen credentials on KeyBank’s real site.
Notably, the criminals added a second page that asks for the user’s multi-factor authentication (MFA) code. If the user has MFA enabled, they’ll receive a prompt after the crooks attempt to log in with the stolen credentials.
While MFA offers a valuable layer of defense, people should know that attackers can still use social engineering to trick them into handing over their MFA codes.
“Multi-factor authentication is still highly recommended, but users should be aware that criminals can directly ask for verification codes while pretending to be the real bank,” Malwarebytes says.
“We should also note that SMS verification is one of the weakest methods for two-factor authentication. Security questions (usually 3 of them) are also used to either reset a password or for some other verification purpose (maybe a login from a new browser or location). This phishing kit also asks the victims to enter that information.”
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Malwarebytes has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
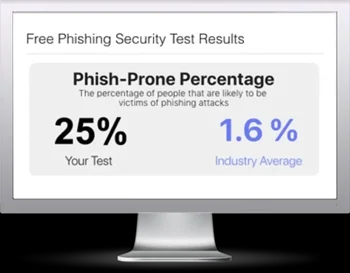
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

