Sophisticated Phishing Campaign Attempts to Bypass SEGs

A widespread phishing campaign is attempting to steal credentials from employees working at dozens of organizations around the world, according to researchers at Group-IB.
The campaign has targeted organizations across twelve industries, including government, aerospace, finance, energy, telecommunications, and fashion.
“The campaign begins with phishing links crafted to mimic trusted platforms commonly used for document management and electronic signatures, such as DocuSign,” Group-IB says.
“Cybercriminals replicate the appearance of legitimate DocuSign emails, complete with branding, logos, and professional formatting. The email might have a subject line like “Complete with DocuSign modified contract” and prompts the recipient to click on a link to view and sign a document, creating the illusion of a routine and trustworthy request.”
The attackers are using legitimate domains to deliver their malicious links, increasing the likelihood that they won’t be detected by Secure Email Gateways (SEGs).
“In a more sophisticated approach, threat actors leverage well-known and trusted domains, such as Adobe.com, to deliver their phishing links,” the researchers write. “One of the primary reasons threat actors use trusted domains is to bypass SEGs and spam filters, which are designed to block suspicious or unknown domains. However, SEGs are less likely to flag URLs that belong to reputable platforms because these domains have established a history of trustworthiness.”
Notably, this campaign automatically extracts the domain and company name from the targeted victim’s email and uses this information to “dynamically update elements on the webpage, such as the favicon, logos, and titles, creating a customized phishing page that mimics the victim’s company for enhanced credibility and deception.”
New-school security awareness training can give your organization an essential layer of defense against social engineering attacks. KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Group-IB has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
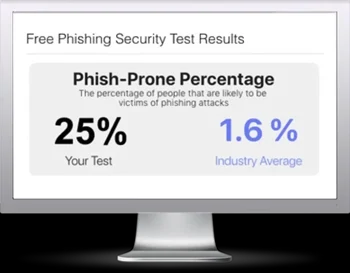
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

