Tax-Themed Phishing Campaign Delivers Malware Via Microsoft Management Console Files

Securonix warns that tax-themed phishing emails are attempting to deliver malware via Microsoft Management Console (MSC) files.
“The attack likely starts with either a phishing email link or attachment,” the researchers explain.
“While we were not able to obtain the original phishing email used in the attack, the lures and nomenclature used in the filenames and lure documents suggest that the campaign follows standard tax-themed phishing methods (Income-Tax-Deduction-and-Rebates202441712.pdf for example).
All of the documents examined are in English and one of them is a general tax document that appears to be prepared by the government of Pakistan.”
This particular attack is targeting users in Pakistan, but the researchers note that the use of .msc files in phishing attacks is starting to pick up traction more broadly.
“Threat actors can exploit these .msc files because of their ability to execute embedded scripts or commands under the guise of legitimate administrative tools,” the researchers explain. “In this scenario we observed the use of JavaScript, though the execution of VBScript is also supported. Therefore, any malicious code executed through the .msc file will execute under the context of mmc.exe. The robust flexibility of MMC files can be exploited maliciously since attackers can craft .msc files that, when opened, execute arbitrary code without explicit user consent.”
Securonix recommends that users “avoid downloading files or attachments from external sources, especially if the source was unsolicited.” The researchers add, “Malicious payloads from phishing emails can be delivered as direct attachments or links to external documents to download. Common file types include zip, rar, iso, and pdf.”
New-school security awareness training can give your organization an essential layer of defense against social engineering attacks. KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Securonix has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
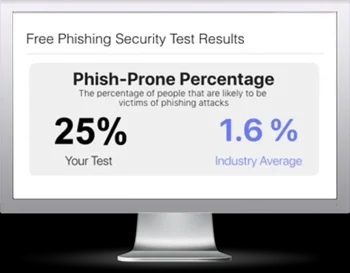
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

