Approaching Ransomware Victims Privately

Researchers at KELA warn that ransomware gangs are increasingly refraining from mentioning their victims’ names after the initial attack, giving the victims a chance to pay up before the attack is publicized. This puts an additional layer of pressure on the victim to pay quickly, because it may allow them to avoid the reputational damage that’s among the biggest threats a victim faces. If the victim refuses to pay, the attackers can then publish their name and threaten to release the stolen data.
“KELA observed a few ransomware groups using relatively new intimidating methods which include publishing a victim without mentioning the company’s name,” the researchers write. “For example, Midas published a few victims claiming ‘a new company’ as their victim on their data leak site. If the victim did not pay, Midas would edit the post and add the victim’s name. Lorenz ransomware gang adopted the same practice and published a ‘new target company’ on their ransomware blog. Additionally, Everest data leak site operators used the same method: a Canada-based supplier was listed with a threat to leak 96 gigabytes of the company’s data, including over 10,500 personal records of Canadian citizens.”
The prolific ransomware gang Conti has adopted a similar tactic, using hidden blog posts to threaten the victims.
“In comparison to Everest and Lorenz who maintain ambiguity regarding victims’ names, Conti’s leaked chats showed that the gang prepared hidden blog posts about victims that can be accessed only via a specific URL,” KELA says. “The actors share this hidden blog post with a victim to intimidate them by showing how easily the victim’s data can be accessed. If a victim agrees to pay, the post is never released; if the negotiation fails, the blog becomes publicly accessible, and the victim’s name is disclosed.”
New-school security awareness training can give your employees an essential layer of defense against ransomware attacks by teaching your employees to thwart phishing and other social engineering attacks.
BleepingComputer has the full story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
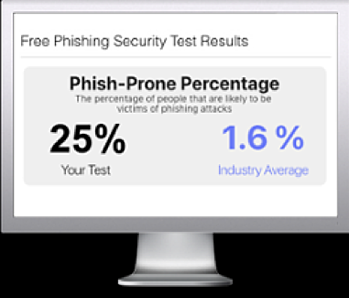
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

