Banking Detail Malvertising Attack Disguises Itself as a Foolproof USPS Google Ad

A new scam aimed at stealing your credit card and banking information has reared its’ ugly head as a completely legitimate ad that is likely to be clicked based on the corresponding search term.
If you type in “USPS Tracking” in Google, you probably want to enter a U.S. Postal Service tracking number so you can see where your package is, right? So, if you saw the following result, would you give it a second thought?
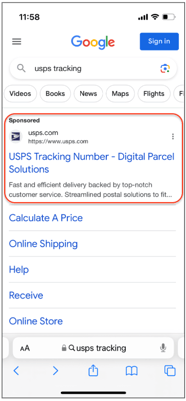
Source: Malwarebytes
You wouldn’t (and neither would I). This is perfect malvertising execution on the part of Ukrainian cybercriminals, according to security researchers at Malwarebytes. What initially seems like a legitimate tracking experience, suddenly changes tone, as the website tells the victim user they must pay a $0.35 fee and asks for credit card information. This alone should raise a red flag. But, since 35 cents isn’t much, let’s assume you go with it – your credit card details will likely be sold off on the dark web.
The real goal of this attack comes next; in an attempt to “verify” your card (under a second brand impersonation of Visa’s “Identity Check” (which I can only assume is trying to appear like their cardholder verification service), the scammers ask the victim to provide their logon credentials to their bank.
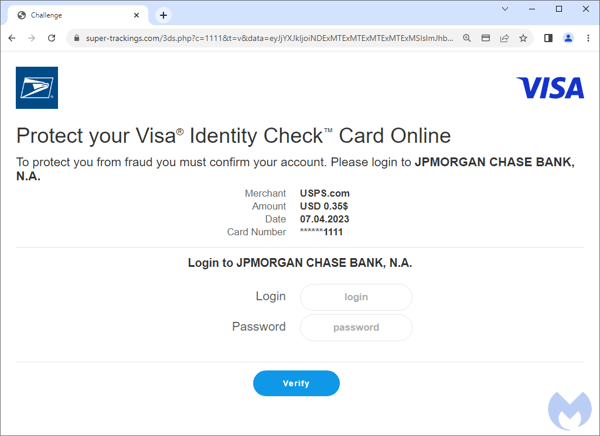
Source: Malwarebytes
Note that the bank and credit card name changes based on the information provided by the victim. It’s a slick attack. But it’s also one that includes unexpected requests – something users who undergo Security Awareness Training should instantly recognize for a cyber attack.
Free Ransomware Simulator Tool
Threat actors are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 24 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
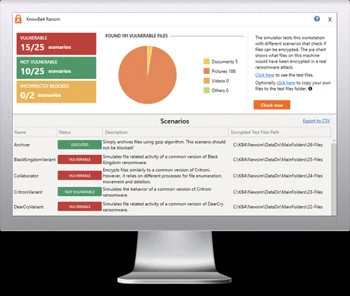
Here’s how it works:
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 25 types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/ransomware-simulator-tool-partner?partnerid=001a000001lWEoJAAW

