Browser-based Phishing Attacks Increase By 198% Over Six Months

Researchers at Menlo Security observed a 198% increase in browser-based phishing attacks over the past six months.
“Attackers have developed tools to craft high quality large scale attacks that target the browser,” the researchers write. “Cybercrime tools, such as phish kits (PhaaS) and ransomware-as-a-service kits (RaaS), have simplified the process of launching sophisticated attacks. These kits provide attackers with pre-made templates, scripts, and resources lowering the bar to craft and deploy their malicious campaigns. Tools like this also make it easier for rudimentary attackers to create convincing and fraudulent websites or emails for the purpose of stealing sensitive information from its intended victims.”
The report highlights a type of phishing attack that uses trusted URLs to bypass security filters.
“Legacy URL Reputation Evasion (LURE) is a growing evasive phishing technique that specifically targets browsers to bypass web categorization of commonly deployed security tools like secure web gateways and URL reputation filters,” the researchers write.
“Threat actors capitalize on this technique by hijacking trusted sites, or by creating a new site and leaving it dormant until its URL/domain is trusted. They then use these URLs and destination sites to launch phishing attacks. This has been a consistent trend during 2023. During such an attack, the user opens the web URL believing it to be authentic. Because the URL is in a safe category, it is neither blocked by the SWG, nor URL filters. The user is subsequently compromised, either with malware or because they are induced to enter their credentials.”
New-school security awareness training can give your organization an essential layer of defense against phishing and other social engineering attacks. KnowBe4 enables your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Menlo Security has the story.
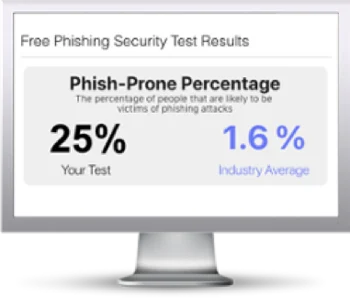
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

