Cryptocurrency Drainer Distributed Through Phishing

Mandiant has published a report on “CLINKSINK,” a cryptocurrency Drainer-as-a-Service (DaaS) that’s targeting users of the Solana currency.
Mandiant’s own X (formerly Twitter) account was hacked earlier this month and used to distribute a link to the drainer. Threat actors using CLINKSINK have stolen at least $900,000 worth of cryptocurrency in recent weeks.
“Numerous actors have conducted campaigns since December 2023 that leverage the CLINKSINK drainer to steal funds and tokens from Solana (SOL) cryptocurrency users,” the researchers explain. “Drainers are malicious scripts and smart contracts that actors can leverage to siphon funds and/or digital assets, such as non-fungible tokens from victims’ cryptocurrency wallets after they are tricked into approving transactions.”
Threat actors are distributing the drainer via phishing links posted to various social media and messaging apps.
“In some recently observed campaigns, threat actors used social media and chat applications, including X and Discord, to distribute cryptocurrency-themed phishing pages that entice victims to interact with the CLINKSINK drainer,” Mandiant says.
“The observed CLINKSINK phishing domains and pages have leveraged a wide range of fake token airdrop-themed lures masquerading as legitimate cryptocurrency resources, such as Phantom, DappRadar, and BONK. These phishing pages have loaded the malicious CLINKSINK JavaScript drainer code to facilitate a connection to victim wallets and the subsequent theft of funds. When a victim visits one of these phishing pages, they are lured into connecting their wallet in order to claim a token airdrop. After connecting their wallet, the victim is then prompted to sign a transaction to the drainer service, which allows it to siphon funds from the victim.”
Mandiant adds that “the apparent leak of the CLINKSINK source code could enable additional threat actors to conduct their own independent draining operations and/or set up further DaaS offerings for others to use.”
KnowBe4 enables your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Mandiant has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
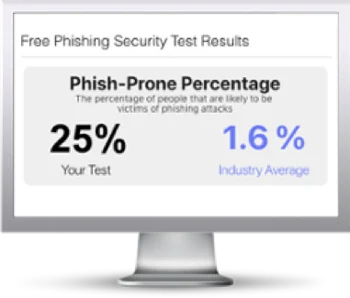
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

