Cryptominers are Tricked out of Cryptocurrency Using Phishing Scams Involving the Purchase of Mining Equipment
The leveraging of Google Docs, a spoofed website, a realistic-feeling buying process, and asking for payment in cryptocurrency is all it takes to separate victims from thousands of dollars.
Despite news stories around phishing attacks resulting in stealing computer processing time for cryptomining, there are legitimate businesses out there that mine cryptocurrency to make money; it’s a simple business really – purchase needed hardware and use it to mine specific cryptocurrency that yields a positive return.
The one piece of hardware that’s most needed is the high-end video card; it’s internal processor is used to perform the calculations that represent the actual “mining”. Cryptomining is so widespread as a money-making operation that such video cards are hard to come by, driving up prices and lowering availability of inventory.
Security researchers at Kaspersky have identified a new scam that targets those involved with cryptomining. Using Google Docs to tag and notify a potential victim, scammers impersonate a legitimate mining hardware vendor, Bitmain.
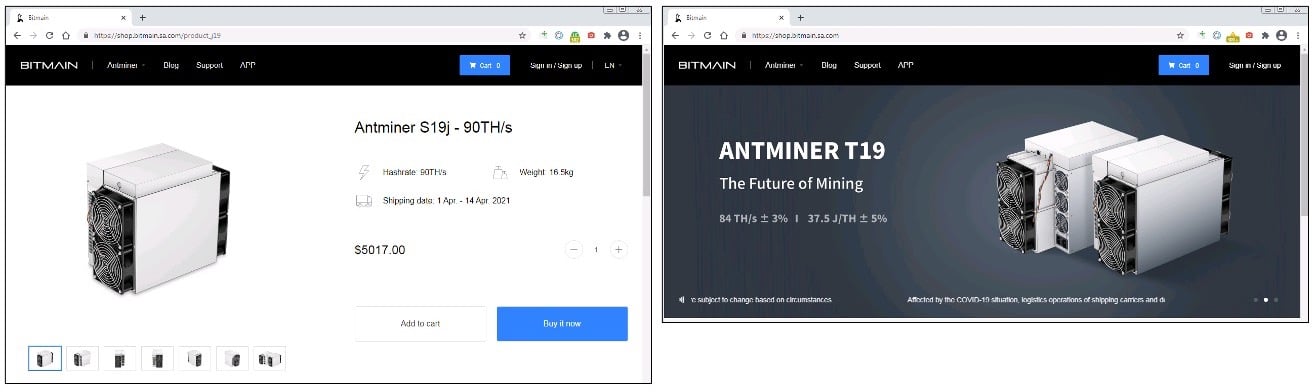
Bitmain’s website (left) and the impersonated site (right)
Source: Kaspersky
This scam uses a well built and functional spoofed website made to look like the real Bitmain site – including shopping cart, checkout process, etc. Because of the convincing nature of the site, scammers trick victims into purchasing hardware that doesn’t exist (and, in real life, it’s not available anywhere due to demand). The kicker to the transaction is victims are only able to pay for the fake hardware using cryptocurrency, with the cybercriminals providing cryptowallet details and a warning that the transaction must be completed within two hours or it will be cancelled.
Once the transaction is complete, the digital currency is gone, the users “account” on the faux Bitmain page is deactivated, and the scam is complete.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

