Energy Sector Experiences Three Times More Operational Technology Cybersecurity Incidents Than Any Other Industry

While industries like financial services and healthcare tend to dominate in IT attacks, the tables are turned when looking at Operational Technology (OT) cyber attacks – and the energy sector is the clear “winner.”
We spend a lot of time talking about attacks that largely impact IT systems. But OT environments are a growing concern as new targets for cybercriminals.
Containing plenty of intellectual property and a clear opportunity for threat actors to hold operations hostage as part of an OT-centric ransomware attack, OT environments are just as critical and require the same level of cybersecurity focus.
According to Rockwell Automation’s Anatomy of 100+ Cybersecurity Incidents in Industrial Operations report, one specific industry stands out from the rest as the largest target of cyber attacks. The Energy sector experienced 39% of all OT cybersecurity incidents, dwarfing the other sectors with the next largest sector (Critical Manufacturing) only experiencing 11% of incidents.
According to Rockwell, these incidents have some common factors:
- 84% of attacks began with the compromise of an IT system
- 60% of attackers are nation-state affiliated groups
- Insiders play an “indirect” role in more than one-third of incidents, which Rockwell attributes to “becoming a victim of a phishing attack”
- The number one initial attack vector is spear phishing attachments (experienced in 34% of attacks)
In the report, Rockwell makes a few recommendations to minimize the risk of attack based on the report data – these include:
- Keeping IT and OT networks segmented and air-gapped
- Leverage Zero Trust technologies
- Monitor for threats 24/7
- Providing ongoing employee security awareness training
KnowBe4 enables your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
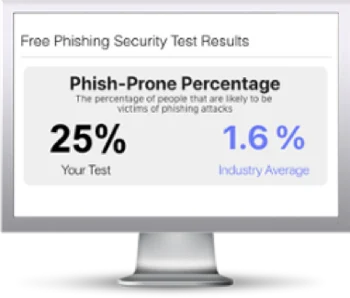
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

