Extremely Persistent Threat Group Demonstrates a Strong Understanding of the Modern Incident Response Frameworks

A threat actor tracked as “Muddled Libra” is using the 0ktapus phishing kit to gain initial access to organizations in the software automation, business process outsourcing, telecommunications, and technology industries, according to researchers at Palo Alto Networks’ Unit 42.
“Muddled Libra investigations demonstrate the use of an unusually large attack toolkit,” the researchers write. “Their arsenal ranges from hands-on social engineering and smishing attacks to proficiency with niche penetration testing and forensics tools, giving this threat group an edge over even a robust and modern cyber defense plan. In the incidents the Unit 42 team has investigated, Muddled Libra has been methodical in pursuing their goals and highly flexible with their attack strategies. When an attack path is blocked, they have either rapidly pivoted to another vector or modified the environment to allow their favored path.”
After gaining access to an organization’s network, the group is extremely persistent.
“The Muddled Libra threat group has also repeatedly demonstrated a strong understanding of the modern incident response (IR) framework,” the researchers write. “This knowledge allows them to continue progressing toward their goals even as incident responders attempt to expel them from an environment. Once established, this threat group is difficult to eradicate. Muddled Libra has shown a penchant for targeting a victim’s downstream customers using stolen data and, if allowed, they will return repeatedly to the well to refresh their stolen dataset. Using this stolen data, the threat actor has the ability to return to prior victims even after initial incident response. This demonstrates the attacker’s tenacity even after initially being discovered.”
The threat actor is also able to use their access to launch supply-chain attacks against their victims’ clients.
“Furthermore, Muddled Libra has appeared to have clear goals for their breaches versus just capitalizing on opportunistic access,” Unit 42 says. “They’ve rapidly sought and stolen information on downstream client environments and then used it to pivot into those environments. They have demonstrated a strong understanding of their victims’ high-value clients and what information would be most useful for follow-on attacks.”
New-school security awareness training can enable your employees to thwart phishing attacks so they can prevent threat actors from gaining access to your environment.
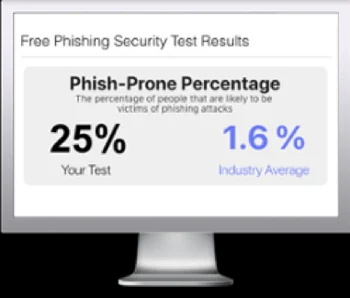
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

