London NatWest Bank Warns Customers of Alarming Impersonation Scams

National Westminster Bank, the London-based bank familiarly known as NatWest, has warned its customers to be on the alert for emails pretending to be from NatWest, but which in fact are from scammers trying to bubble the unwary out of their savings.
The imposture proceeds like this: a NatWest customer receives an email telling them that the mobile number associated with their account has been successfully changed, and that a one-time passcode has been sent to the customer’s old phone number so they may conveniently complete the process of switching. Naturally the customer hasn’t switched the mobile number associated with their bank account. They’re probably inclined to click the link in the email that helpfully offers to enable them to cancel the perhaps mistaken, certainly unwanted, transaction.
That link will take the victim to a fairly convincing but bogus NatWest page that (naturally) asks for the customer’s user ID and password. And of course should the customer provide these, the account is compromised.
While the bogus page looks fairly convincing, there are still issues with the email that should alert a user. First, as NatWest points out in warnings it’s distributed, genuine emails from them are always personalized. That is, the scammers greet the mark as “Dear Customer,” whereas NatWest would address you by name. That’s not definitive assurance that an email is genuine, but in this case it’s an indication. Second, there are usage and formatting errors in the phishing email, like those in the key phrase “Online Bankingservices.” And, finally, the domain is off. The phish bait comes from the phony domain “@natwestsecure.com” as opposed to the genuine “@natwest.com.”
It’s a familiar story, but it bears repeating. The scams being reported here are threats to personal bank accounts, but there’s no reason the tactics couldn’t be used against businesses or other organizations as well. New-school security awareness training can help prepare the user’s mind to resist exactly this sort of social engineering.
The publication “Which” has the story.
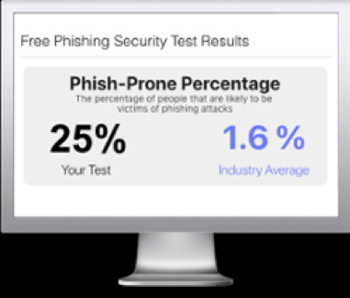
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

