Malicious Office Documents Jump to 37% of All Malware Downloads at the End of 2021

With the ubiquitous use of Microsoft Office today, it should come as no surprise that malicious macro-laden documents continue to reign, with PPT files delivering AgentTesla taking the spotlight.
At this point, every security professional should be keenly aware that malicious macros stored within Office files are a powerful tool for threat actors. Using impressive obfuscation techniques that keep security solutions from detecting the malicious intent of an Office attachment in an email, these attackers are seeing great successes that have caused the use of Office documents to jump from just 19% in the beginning of 2020 to nearly double, at 37% at the end of 2021, according to NetSkope’s Cloud and Threat Report – January 2022.
But a recent blog from NetSkope highlights how a PowerPoint file is used to deliver the AgentTesla remote access trojan and other malware. The obfuscation techniques are many – from decrypting internal strings at runtime, to using Outlook to launch PowerShell, to continuing to live off the land using MSHTA and VBA, to the encoded VB script needed being hidden within an HTML page.
And that’s just, in essence, the dropper portion of the attack. The folks that built this have spent some serious time ensuring this doesn’t get detected.
But what really makes this attack powerful is the participation of the recipient user who falls for the phishing scam and opens the PPT file to begin with:
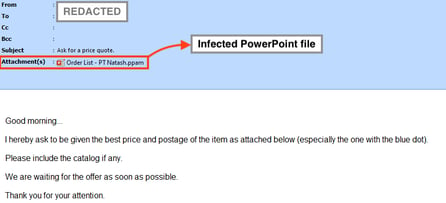
Source: NetSkope
When you look at it here, the email isn’t particularly compelling. And yet, people fall for it.
Your users aren’t as vigilant as you are; they need continual education through Security Awareness Training to ensure they remember “oh, this could be malicious – I shouldn’t open it” when the time comes to test their cyber-smarts.
PPTs have been used before, so this isn’t exactly new. But that’s what’s scary – you’d think by now no one would fall for a malicious PPT sent in an email… and yet they do.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

