Malvertising With Google Ads

Researchers at Malwarebytes warn that a large malvertising campaign is exploiting Google ads to redirect users to phishing sites.
“[W]e recently uncovered a malvertising chain abusing Google’s ad network to redirect visitors to an infrastructure of tech support scams,” the researchers write. “Unsuspecting users searching for popular keywords will click an advert and their browser will get hijacked with fake warnings urging them to call rogue Microsoft agents for support.
What makes this campaign stand out is the fact that it exploits a very common search behavior when it comes to navigating the web: looking up a website by name instead of entering its full URL in the address bar.”
The attackers are buying ads related to popular search terms, so that users will see the malicious ads at the top of their search results. The top search terms the attackers are targeting are “Youtube,” “Facebook,” “Amazon,” and “Walmart.”
The ads also display the legitimate URL of the targeted site, and will show a Google ad URL if the user hovers over it. As a result, users won’t see a suspicious URL until after they’ve clicked the link.
“The threat actors are abusing Google’s ad network by purchasing ad space for popular keywords and their associated typos,” the researchers write. “A common human behavior is to open up a browser and do a quick search to get to the website you want without entering its full URL.
Typically a user will (blindly) click on the first link returned (whether it is an ad or an organic search result). Let’s say you want to load YouTube and type ‘youtube’ instead of entering the full address ‘youtube.com’ in the browser’s address bar. The first result that appears shows ‘www.youtube.com’ so you are likely to trust it and click on it.”
New-school security awareness training can teach your employees to follow security best practices so they can avoid falling for social engineering attacks.
Malwarebytes has the story.
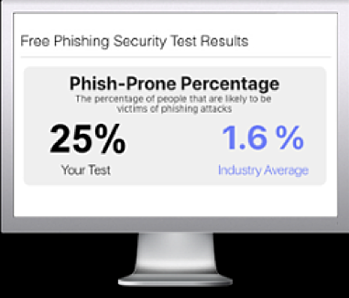
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

