MFA Defenses Fall Victim to New Phishing-As-A-Service Offerings

ZeroFox warns that phishing-as-a-service (PhaaS) offerings are increasingly including features to bypass multi-factor authentication.
“In 2023, ‘in-the-middle’ techniques are some of the most frequently-observed methods used to gain access to MFA-secured networks,” the researchers write.
“They enable threat actors to intercept or bypass MFA protocols by stealing communications without the victim’s knowledge. Threat actors create and exploit new sessions, or intercept existing ones, via session hijacking—including the stealing or selling of cookies and authentication tokens—session fixation, or session cloning.
Exploiting vulnerabilities at the application and network layers can grant threat actors access to an authenticated session, undermining MFA protocols. Attackers can seize control of session permissions and parameters, facilitating greater opportunity for exploitation and detection avoidance.”
A significant amount of phishing emails are used to deliver malware, particularly ransomware.
“Malicious email attachments will very likely remain one of the most prevalent means of malware distribution for the foreseeable future,” ZeroFox says.
“Reporting states that malicious attachments are leveraged in approximately 40 percent of phishing attacks and have been responsible for the delivery of 35 percent of ransomware so far in 2023—the highest of any delivery method.
Despite security controls being regularly updated to account for these file types—ensuring suspicious files are flagged to end users—it is very likely threat actors will continue to pivot to file types that circumvent security controls.”
The researchers note that attackers are using a variety of different file types and techniques to distribute malware.
“Threat actors increasingly leverage files such as Windows image files (ISO), archive files (RAR), Windows Shortcut files (LNK), OneNote files, restricted permission messages (RPMSG) files, and Windows Script files to deploy malicious payloads,” the researchers write.
“Threat actors have also been observed leveraging HTML smuggling to deliver prominent malware strains such as QBot and Emotet, whereby threat actors conceal a malicious script inside these files that is able to assemble and embed itself on the target network upon activation. This avoids malicious code being passed over the network.”
New-school security awareness training can give your organization an essential layer of defense by enabling your employees to thwart social engineering attacks.
ZeroFox has the story.
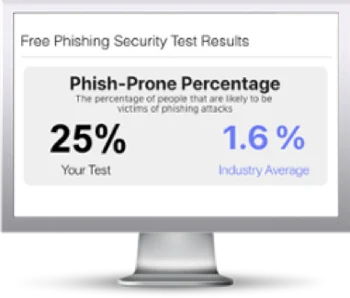
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

