Microsoft Azure’s Static Web Apps Service Becomes the New Home for Phishing Attacks

Taking advantage of the value of a legitimate web service, along with a valid SSL certificate, a new campaign of phishing attack targeting online Microsoft credentials is leveraging Azure.
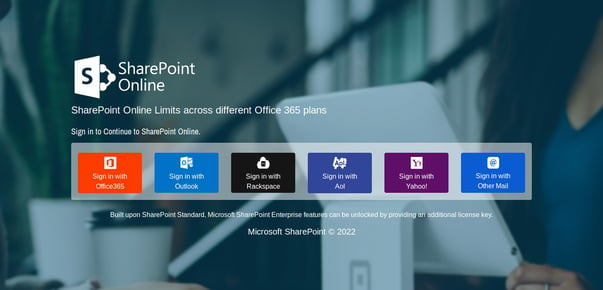
Microsoft Azure’s App Service empowers organizations to quickly create and deploy web-based apps. But a new use for this service was recently identified by the analysts at MalwareHunterTeam. On their Twitter account (shown below), they posted the finding of a set of threat actors using the service’s legitimacy to help get malicious content focused on stealing OneDrive, Microsoft 365, Outlook.com, Rackspace, Aol, and any other online mail platform’s credentials.
Did you heard about “Azure Static Web Apps” yet? If no, let me explain to you in short what is that: it is another service from Microsoft for actors to help them phish their own customers / users…
😂
😫
A fresh example: https://agreeable-dune-0b7a9100f.1.azurestaticapps[.]net/ pic.twitter.com/gwf7YdG3Fx— MalwareHunterTeam (@malwrhunterteam) March 30, 2022
These attacks likely work in conjunction with a phishing attack that gets the victim to want to see the contents of a weblink, and then – using realistic spoofed logon pages – asks the victim to “logon” to steal their credentials.
These kinds of attacks are relatively simple to spot, if the user in question has undergone continual Security Awareness Training that not only educates them on tactics like the ones used in this attack, but also elevates their sense of awareness so they will scrutinize a logon page like the one above and quickly come to the same conclusion that every IT pro does instantly when seeing it – it’s a scam.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

