Mobile Phishing Campaign Targets Job Seekers

Researchers at Zimperium warn that a phishing campaign is targeting Android phones to deliver the Antidot banking trojan.
The attackers are impersonating recruiters to target job seekers with phony employment offers. They use well-crafted phishing emails that purport to come from real companies, informing recipients that they’ve been selected to advance in the hiring process.
“The attackers behind this phishing campaign demonstrated a remarkable level of adaptability, leveraging diverse and sophisticated social engineering strategies to target their victims,” the researchers write.
“A key tactic employed by the attackers involves masquerading as a job recruiter or HR representatives from well-known organizations. Victims are enticed to respond to fraudulent emails, carefully crafted to resemble authentic job offers or requests for additional information.”
Once installed on a phone, the malware is designed to compromise 95 banking apps and 62 cryptocurrency apps. It can also steal other information from the phone, posing a threat to companies whose employees use their phones for work.
“As part of their fraudulent hiring process, the phishing campaign tricks victims into downloading a malicious application that acts as a dropper, eventually installing the updated variant of Antidot on the victim’s device, which we call AppLite Banker,” Zimperium says.
“Beyond its ability to mimic enterprise companies, the Banker also masquerades as Chrome and TikTok apps, demonstrating its wide-ranging target vectors, including full device take-over and application access. The level of access provided the attackers could also include corporate credentials, applications, and data if the device was used by the user for remote work/access for their existing employer.”
New-school security awareness training can give your organization an essential layer of defense by teaching your employees to recognize social engineering attacks. KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Zimperium has the story.
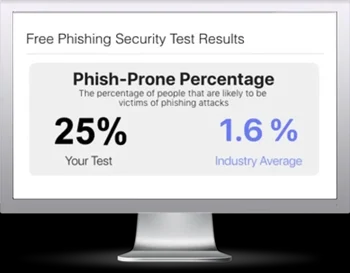
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

