New Cyberattack Campaign Delivers Multiple RATs via Trusted Cloud Services

Abusing cloud providers including Microsoft Azure and AWS, cybercriminals are setting up malicious infrastructure to hide their operations and avoid detection.
There are two parts to this story about a new cyberattack spotted in the wild by Cisco Talos – first, cybercriminals are leveraging the fast deployment of infrastructure within both Microsoft’s and Amazon’s cloud environment. And second, the attacks don’t just leverage one remote access trojan (RAT) as the payload, but three different RATs.
The use of public cloud infrastructure is smart – it makes it difficult for security solutions to easily identify attacks immediately as being malicious. The hosting mixed with complex obfuscation techniques in the downloader scripts – which have been seen executed as JavaScript, batch file, or VBScript – make it increasingly difficult.
The use of multiple RATs – Nanocore, Netwire, and AsyncRAT, to be specific – signifies the cybercriminals are privy to understanding that they need to use the right tool for the job at hand. Nanocore is a small 32-bit .NET portable executable. Netwire is a data-stealing trojan, and AsyncRAT is focused on remotely monitoring and controlling computers.
This level of advanced execution demonstrates how cybercriminals are really thinking their attacks through, carefully considering how they might be detected, and taking great strides to avoid detection while delivering just the right payload to accomplish the remainder of their malicious actions.
According to Talos, the attacks all start with a simple phishing campaign using a malicious ZIP file as the attachment.
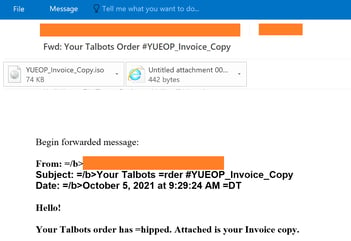
Source: Talos
That’s good news. Any employee that has undergone Security Awareness Training will easily identify that an HTML attachment isn’t going to be used as an invoice – ever. It’s these small indicators of malice that users who undergo training begin to store away and use continually as they interact with email and the web – all to spot a suspicious or malicious attack and stop it by not engaging, before any harm can be done.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

