New “Greatness” Phishing-as-a-Service Tool Aids in Attacks Against Microsoft 365 Customers

This new phishing toolkit is rising in popularity for its effective realism in impersonating not just Microsoft 365, but the victim organization as well.
Security researchers at Cisco Talos have identified a new Microsoft 365 toolkit that actually creates a realistic login experience for the victim user, making it more dangerous to organizations.
The convincing impersonated login pages include:
- Microsoft 365 branding and look-alike login page content
- The victim’s email address pre-filled
- The victim organization’s logo and background image (extracted from their real Microsoft 365 login page)
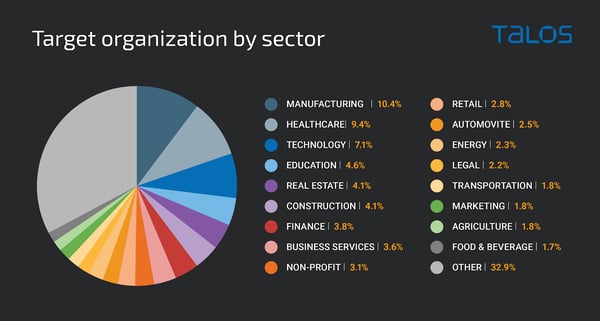
According to Cisco Talos, the target victim organizations were almost exclusively in the U.S., U.K., Australia, South Africa, and Canada, with the most commonly targeted sectors being manufacturing, healthcare and technology.
Source: Cisco Talos
The attack actually does more than simply present the victim with a login page or ask them to enable macros. This sophisticated toolkit grabs a blurred image of an Excel spreadsheet with a superimposed box hosting a Microsoft 365 logo and a spinning wheel (as if to convey the document is trying to load). The victim is then presented with a Microsoft 365 login page already sitting at the “enter your password” stage:
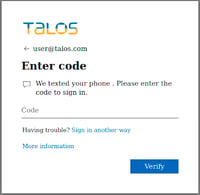
Source: Cisco Talos
Upon password entry, the toolkit attempts a login, and should multi-factor authentication (MFA) be enabled, performs a passthrough MFA attack, where the toolkit says **it is** sending the victim a code to their phone (when, in fact, Microsoft 365 is doing it). Once the code is entered into the toolkit, the code is passed through to perform the legitimate logon, giving attackers access to the Microsoft 365 account.
If there was ever a need for security awareness training to teach users to be mindful when interacting with unexpected inbound email that involves even the most believable user experience, this attack makes it clear that the time is now.
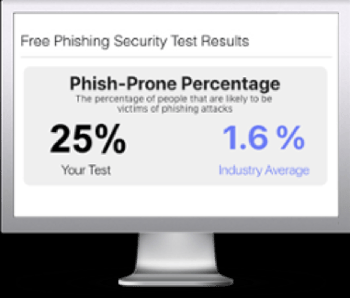
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

