New LinkedIn-Impersonated Phishing Attack Uses Bad Sign-In Attempts to Harvest Credentials

With compromised LinkedIn credentials providing cybercriminals with ample means to socially engineer business contacts, this campaign is a stark warning for organizations.
The power of impersonation is demonstrated in this latest attack detailed by the security analysts at ArmorBlox. Using a mixture of social engineering cues, valid SPF and DMARC checks, and a spoofed logon page, the threat actors behind this campaign targeted a national travel company to steal LinkedIn credentials.
According to ArmorBlox, the campaign starts with an email purporting to come from LinkedIn (although the actual email shows it’s not) informing the recipient of a bad logon attempt.
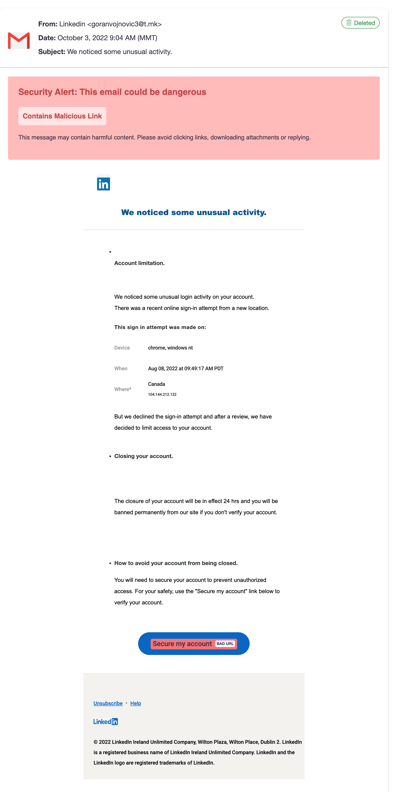
The call to action of securing their account is enough to create a sense of urgency in the victim to want to take control of the situation and respond accordingly – in this case, by clicking the link.
Upon clicking, the victim is presented an impersonated LinkedIn logon page, shown below:
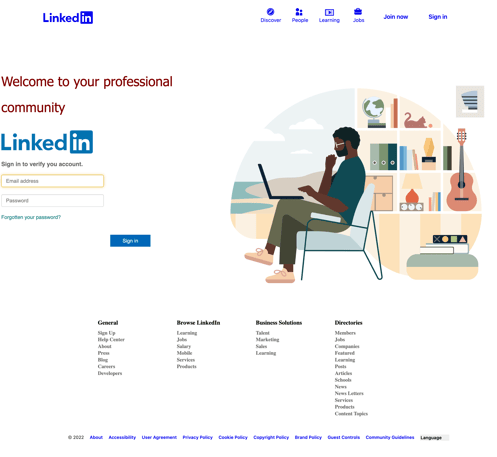
It’s evident some thought was put into the presentation of this page to make it appear legitimate. The victim user is prompted to provide their credentials to verify their identity and “secure” the account.
The ramifications of this attack being successful are likely a ripple effect of subsequent social engineering attacks until just the right victim organization is found.
With such blatant signs of this being bogus right from the beginning, no user should fall for this scam. However, in the rush of the business day, it’s conceivable that users will fall for this – that is, if they aren’t continually operating in a state of vigilance when interacting with email. This vigilant state is achievable by putting employees through continual Security Awareness Training.
Don’t get hacked by social media phishing attacks!
Many of your users are active on Facebook, LinkedIn, and Twitter. Cybercriminals use these platforms to scrape profile information of your users and organization to create targeted spear phishing campaigns in an attempt to hijack accounts, damage your organization’s reputation, or gain access to your network.
KnowBe4’s Social Media Phishing Test is a complimentary IT security tool that helps you identify which users in your organization are vulnerable to these types of phishing attacks that could put your users and organization at risk.
Here’s how the Social Media Phishing Test works:
- Immediately start your test with your choice of three social media phishing templates
- Choose the corresponding landing page your users see after they click
- Show users which red flags they missed or send them to a fake login page
- Get a PDF emailed to you in 24 hours with your percentage of clicks and data entered
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/social-media-phishing-test-partner?partnerid=001a000001lWEoJAAW

