New Phishing Campaign Uses Hyperlinked Images for Fake Gift Cards and Promotions

A phishing campaign is using hyperlinked images in order to trick users into visiting malicious sites, according to Jeremy Fuchs at Avanan. The emails contain images that offer gift cards or promotions for Delta or Kohls.
“Obfuscation is a gift to hackers,” Fuchs says. “It allows them to pull off a magic trick. It works by hiding the true intent of their message. In this case, it’s a picture. The picture is meant to entice the user to click. Who wouldn’t want a $1,000 Delta Gift Card? They hope the user will be intrigued enough not to hover over the URL and see that it doesn’t match. An eagle-eyed user would see that and immediately know something is amiss.”
Fuchs notes that many legitimate promotional emails use these types of linked images, so users are less likely to check the actual URL.
“Behind the picture is the URL—even legitimate brand pictures link to a page,” Fuchs says. “Most marketing emails work that way. There will be a nice-looking promotional image, and the link will go to the intended page. However, the intended page has nothing to do with Delta or Kohl’s and everything to do with stealing your information.”
The emails may also bypass security scanners since the emails don’t contain any text.
“[T]hey’re also hoping that the URL filters will be confused too,” Fuchs writes. “It’ll look clean if they aren’t scanning within the image. This is a fairly common method. Often, hackers will happily link a file, image, or QR code to something malicious. You can see the true intention by using OCR to convert the images to text or parsing QR codes and decoding them. But many security services don’t or can’t do this.”
New-school security awareness training can give your employees a healthy sense of suspicion so they can avoid falling for social engineering attacks.
Avanan has the story.
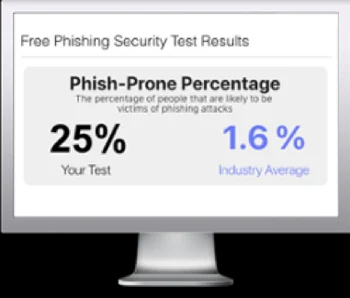
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

