Open Redirects Exploited for Phishing

Attackers are exploiting open redirects to distribute links to credential-harvesting sites, according to Roger Kay at INKY. The attackers are exploiting vulnerable American Express and Snapchat domains to launch the attacks. American Express has since fixed the vulnerability, but Snapchat’s domain remains unpatched.
“From mid-May through late July, INKY detected many instances of bad actors sending phishing emails that took advantage of open redirect vulnerabilities affecting American Express and Snapchat domains,” Kay writes. “Open redirect, a security vulnerability that occurs when a website fails to validate user input, allows bad actors to manipulate the URLs of high reputation domains to redirect victims to malicious sites. Since the first domain name in the manipulated link is in fact the original site’s, the link may appear safe to the casual observer. The trusted domain (e.g., American Express, Snapchat) acts as a temporary landing page before the surfer is redirected to a malicious site.”
The phishing emails impersonate DocuSign, FedEx, and Microsoft, and the links lead to a spoofed Microsoft login page. The threat actors also used stolen personal information to tailor the attacks to individual users.
“In both the Snapchat and the American Express exploits, the black hats inserted personally identifiable information (PII) into the URL so that the malicious landing pages could be customized on the fly for the individual victims,” Kay says. “And in both, this insertion was disguised by converting it to Base 64 to make it look like a bunch of random characters. We inserted our own random characters into these strings so that the casual observer would not be able to reverse engineer the PII strings.”
Kay offers the following advice to help users recognize these links.
“When examining links, surfers should keep an eye out for URLs that include, for example, ‘url=’, ‘redirect=’, ‘external-link’, or ‘proxy’,” Kay says. “These strings might indicate that a trusted domain could redirect to another site. Recipients of emails with links should also examine them for multiple occurrences of “http” in the URL, another potential indication of redirection.”
New-school security awareness training can enable your employees to thwart phishing attacks by teaching them how to recognize social engineering tactics.
INKY has the story.
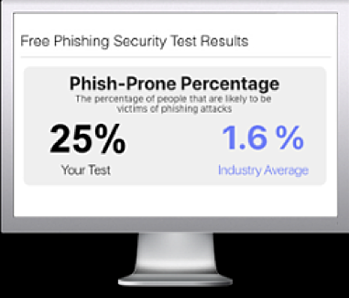
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

