Phishing Attacks Abuse Microsoft 365 to Bypass Security Filters

Threat actors are abusing Microsoft’s infrastructure to launch phishing attacks that can bypass security measures, according to researchers at Guardz.
The attackers compromise multiple Microsoft 365 tenants in order to generate legitimate transaction notifications that contain phishing messages.
“This attack exploits legitimate Microsoft services to create a trusted delivery mechanism for phishing content, making it difficult for both technical controls and human recipients to detect,” the researchers write.
“Unlike traditional phishing, which relies on lookalike domains or email spoofing, this method operates entirely within Microsoft’s ecosystem, bypassing security measures and user skepticism by leveraging native M365 infrastructure to deliver phishing lures that appear authentic and blend in seamlessly.”
The attackers use Microsoft 365’s built-in tenant display name feature to display the phishing message rather than placing it in the email body. In one case, for example, the attackers set the display name to the following: “(Microsoft Corporation) Your subscription has been successfully purchased for 689.89 USD using your checking account. If you did not authorize this transaction, please call 1(888) 651-4716 to request a refund.”
The researchers explain, “The attacker weaponizes the tenant’s organization name field to inject a phishing lure directly into the email. Instead of embedding malicious links, the message instructs victims to call a fraudulent support number, leading to a social engineering attack designed to lure the victim to install a stealer (malware) / steal financial information or credentials.”
The attackers are using this technique to carry out business email compromise (BEC) attacks. Guardz notes that since the messages tell the victim to call a phone number, the scam is less likely to be stopped by technical security measures.
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Guardz has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
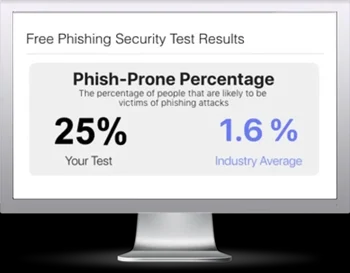
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

