Phishing Attacks Employing QR Codes Are Capturing User Credentials

Using a new twist to bypass detection from security solutions, cyber attacks are now employing what will be construed as a benign image whose malicious intent can’t be traced.
Threat actors need some means of getting a user to engage with malicious content – whether an attachment, link, or phone call, there needs to be some content within an email that provides the victim user with their next step. Right behind this are the security solutions which have employed scanning those attachments, following the links to their end, etc. in an attempt to provide the user and their organization with a first layer of defense to stop such attacks before they start.
A new phishing attack method spotted by security researchers at Inky includes the use of a QR code, prompting a victim user to take a picture of the image and navigate to the resulting impersonated login page.
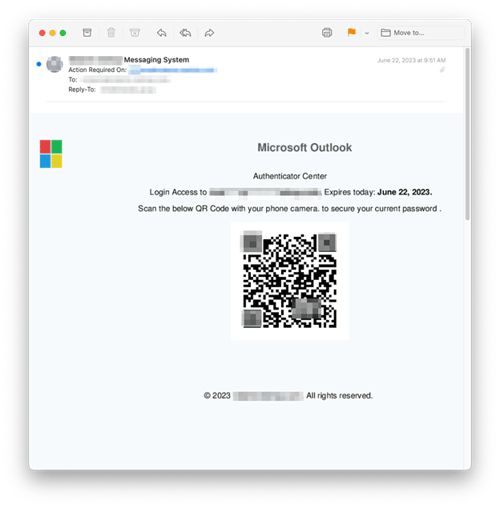
Source: Inky
It’s brilliant for a number of reasons:
- I’m not aware of any security solution that can follow a QR code-based URL to determine if the resulting URL is malicious or not.
- It shifts the actual threat action to another device – specifically one that has far less protections than a user’s endpoint.
But it’s also awkward as well, because who takes a picture of a QR code to login to their email, etc. instead of just clicking a link. Despite this lack of reasoning as to why this should work, I’m certain it does anyway, otherwise the cybercriminals wouldn’t be using this method.
This kind of attack highlights the fact that your users need to be continually educated through Security Awareness Training that anything out of the ordinary – especially something this wacky just to log onto a website – should be avoided.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

