Phishing Campaign Targets YouTube Creators

An email phishing campaign is targeting popular YouTube creators with phony collaboration offers, according to researchers at CloudSEK. The emails contain OneDrive links designed to trick users into installing malware.
“The malware is hidden within attachments such as Word documents, PDFs, or Excel files, often masquerading as promotional materials, contracts, or business proposals,” the researchers explain.
“The phishing emails are sent from spoofed or compromised email addresses, making them seem credible. Recipients are lured into downloading the attached files, believing they are legitimate business offers….Once the attachment is opened, the malware installs itself on the victim’s system. This malware is typically designed to steal sensitive data, including login credentials, financial information, and intellectual property, or to provide remote access to the attacker.”
The threat actors impersonate well-known brands and offer generous compensation in exchange for a 15-second ad spot. The emails are convincingly written in a professional tone.
CloudSEK was able to access the threat actor’s backend infrastructure, and found that they used automation to launch targeted phishing attacks against a large number of YouTube accounts.
“We also discovered a stealer log from the threat actor’s email account, exposing details of the entire campaign,” the researchers write. “This included SMTP email accounts (such as onet.eu and Murena.io), SOCKS5 proxies, Google Cloud APIs, victim emails and cookies, as well as phishing templates.
It appears that a multi-parser tool was used to collect data from YouTube, allowing the threat actor to obtain a large number of email addresses associated with YouTube channels as part of their initial reconnaissance efforts.”
New-school security awareness training can give your organization an essential layer of defense against phishing and other social engineering attacks. KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
CloudSEK has the story.
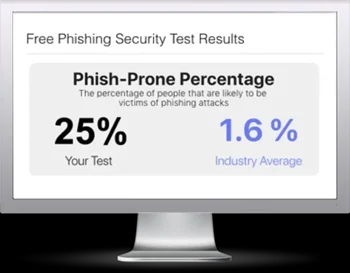
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

