Phishing campaign uses UPS.com XSS vulnerability to distribute malware
A researcher has disclosed details of a clever UPS phishing campaign which utilised an XSS vulnerability in UPS.com to push fake and malicious ‘Invoice’ Word documents. The threat actor has used the XSS vulnerability in UPS.com to modify the site’s regular page to look like a legitimate download page. This vulnerability allowed the threat actor to distribute a malicious document through a remote Cloudflare worker but make it look like it was being downloaded directly from UPS.com.
Dissecting the UPS phishing scam
This email is filled with numerous legitimate links that perform no malicious behavior. However, the tracking number is a link to UPS’ site that includes an exploit for an XSS vulnerability that injects malicious JavaScript into the browser when the page is opened.
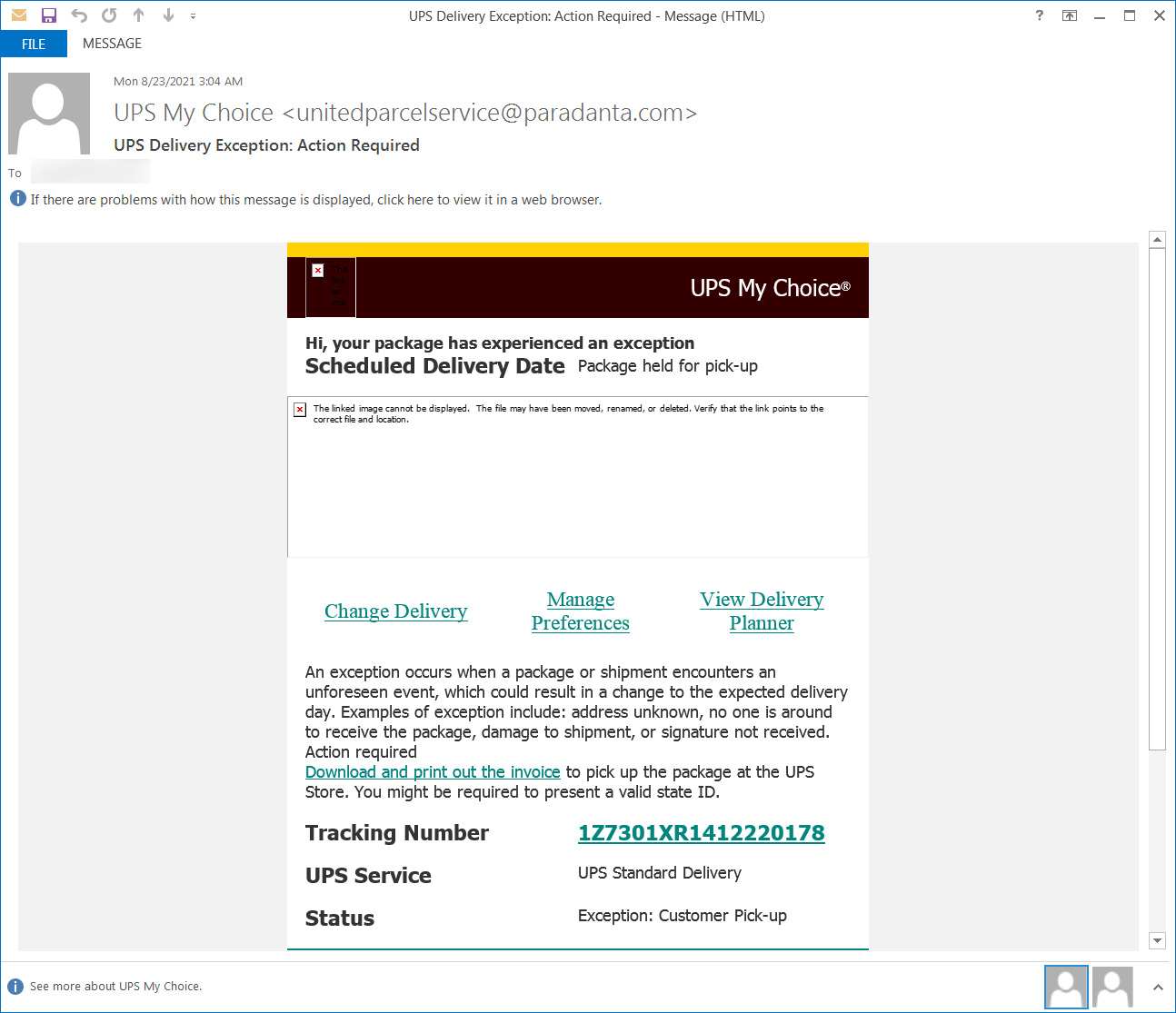
This phishing campaign stands out because a user visiting the URL will see a legitimate ups.com URL prompting a download of an invoice. This tactic will likely cause the victims to open the invoice with less suspicion, thinking it is a real file from UPS. Once the malicious document is opened, a file is downloaded which would have contained the payload. The exact payload in this instance could not be established by the researcher as the URL was no longer working.
The researchers are awaiting a response from UPS but believe that the vulnerability has been fixed. However, this example highlights the constant evolving tactics used by malicious actors to target victims.
New-school security awareness training can create a culture of security within your organization by teaching your employees to follow security best practices and not open these phishing emails.
With thanks to the Cyber Defence Alliance and Bleeping Computer. The full story is here: https://www.bleepingcomputer.com/news/security/phishing-campaign-uses-upscom-xss-vuln-to-distribute-malware/
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

