Phishing Campaigns Continue To Exploit CrowdStrike Outage

As expected, threat actors are taking advantage of the global IT outage caused by a faulty CrowdStrike update last Friday, SC Media reports.
We’ve been covering this story and it looks like the campaigns have only continued. Cybercriminals quickly registered dozens of phishing domains related to the outage, including “crowdstrike-helpdesk[.]com” and “crowdstrikefix[.]com.”
CrowdStrike issued an advisory warning that threat actors are conducting the following activity:
- “Sending phishing emails posing as CrowdStrike support to customers
- Impersonating CrowdStrike staff in phone calls
- Posing as independent researchers, claiming to have evidence the technical issue is linked to a cyberattack and offering remediation insights
- Selling scripts purporting to automate recovery from the content update issue”
CrowdStrike is also tracking a phishing campaign that’s targeting customers in Latin America with Spanish-language instructions to remediate the issue. The threat actor instructs victims to download a file called “crowdstrike-hotfix.zip,” which will install the RemCos remote access trojan.
The US Cybersecurity and Infrastructure Security Agency (CISA), the UK’s National Cyber Security Centre (NCSC), and the Australian Signals Directorate (ASD) have each issued warnings on increased phishing activity. The ASD stated, “An increase in phishing referencing this outage has already been observed, as opportunistic malicious actors seek to take advantage of the situation.”
Security firm Bolster has also observed threat actors setting up domains that impersonate law firms offering to file legal claims against CrowdStrike.
“Given the financial losses likely to be incurred due to the widespread outage, many individuals and businesses may seek to recoup their losses through legal action or government assistance, creating a fresh opportunity for threat actors to strike,” SC Media writes. “Business leaders should remain wary of potential scams such as phony recovery funds or websites impersonating law firms as they work to recover from the incident.”
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
SC Media has the story.
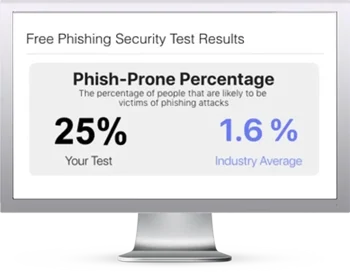
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

