Phishing Kit Targets the FCC and Crypto Exchanges

Researchers at Lookout have discovered a sophisticated phishing kit that’s targeting employees at the US Federal Communications Commission (FCC), as well as employees of cryptocurrency exchanges Binance and Coinbase.
The kit also targets users of cryptocurrency platforms, including Binance, Coinbase, Gemini, Kraken, ShakePay, Caleb & Brown and Trezor.
The phishing kit “enables attackers to build carbon copies of single sign-on (SSO) pages, then use a combination of email, SMS, and voice phishing to trick the target into sharing usernames, passwords, password reset URLs, and even photo IDs from hundreds of victims, mostly in the United States.”
The researchers spoke to some of the victims and learned that the attackers are using phone calls and text messages to target users.
“In one scenario, a victim received an unsolicited phone call that spoofed a real company’s customer support line,” Lookout says. “The person on the other end of the line was the threat actor, but sounded like a member of the support team from that company. They informed the victim that their account had been hacked, but that they would help them recover the account. While the victim was on the phone with the threat actor, they were sent a text message that linked them to the phishing page.”
“While still on the phone with the victim, the threat actor encouraged them and helped them complete the steps. As a way to build credibility and trust, the actor consistently noted that the allegedly unauthorized device accessing the account was in Salt Lake City, Utah. This was mentioned in the text message, the phone call, and on the phishing page itself (which is customizable to display different device types or locations).”
The researchers note that the campaign is ongoing and appears to be successful at stealing credentials.
“Lookout researchers have also been able to gain ephemeral access to the backend logs, where we noted consistently high quality of the stolen credentials,” the researchers write. “Typically, when accessing a phishing site’s data, it is filled with junk data that is obviously not someone’s real email address or password.”
“However, a high percentage of the credentials collected by these sites look like legitimate email addresses, passwords, OTP tokens, password reset URLs, photos of driver’s licenses, and more. The sites seem to have successfully phished more than 100 victims, based on the logs observed. Many of the sites are still active and continue to phish for more credentials each hour.”
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Lookout has the story.
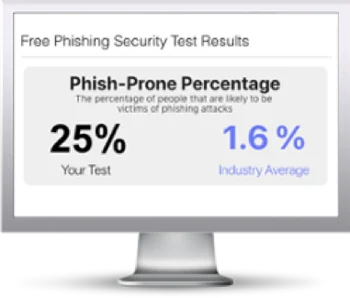
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

