Phishing Tops 2023’s Most Common Cyber Attack Initial Access Method

New analysis shows that the combination of phishing, email, remote access, and compromised accounts are the focus for most threat actors.
Data across the industry corroborates new findings in cyber risk advisory and response firm Kroll’s just-released Q4 2023 Cyber Threat Landscape Report. But what’s interesting in this report is how the data tells a story of where organizations are falling short in their preventative efforts.
First, let’s jump into the findings of where each of the common initial access methods rank. As shown below, while phishing decreased between 2022 and 2023, it still dominates as the most-used method.

Source: Kroll
Interesting to note is the massive jump in the use of Valid Accounts whereby initial access brokers compromise accounts and sell them to threat actors who leverage the accounts as a means of gaining access to an organization. Since we all know how most of those valid accounts were obtained, I’m going to point out that phishing is an even bigger problem.
If we “zoom out” a bit and look at the most common incident threat types, we see ransomware taking a back seat last year to email compromise – again, likely using credential harvesting to obtain credentials.

Source: Kroll
The underlying story here is clear – phishing is the problem. Whether we’re talking about phishing with the intent of compromising credentials to be used later, or phishing used to infect systems and gain access, cybercriminals are leveraging phishing more now than ever.
Your layered defense against these attacks must include a vigilant user; one who has undergone continual security awareness training, who knows what to look for and how to spot a suspicious email.
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Free Phishing Security Test
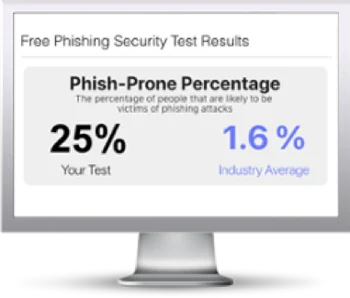
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

