“Picture in Picture” Phishing Attack Technique Is So Simple, It Works

Using credibility-building imagery and creating a need for the user to click what may or may not be perceived as an image is apparently all it takes to engage potential phishing victims.
Phishing attacks only need two things: something to create a sense of urgency and something to establish a sense of credibility. I’ve covered plenty of scams where brand impersonation of brands like Amazon, UPS or Walmart with a notice to take immediate action is all it takes to get a potential victim to respond.
A recent article from security vendor Avanan talks about a “Picture in Picture” attack. While I think the title is a bit misplaced (as there is just a single image used to establish both credibility and urgency), it is still effective enough and warrants being covering.
Take the example below. The email address has nothing to do with Delta Airlines.
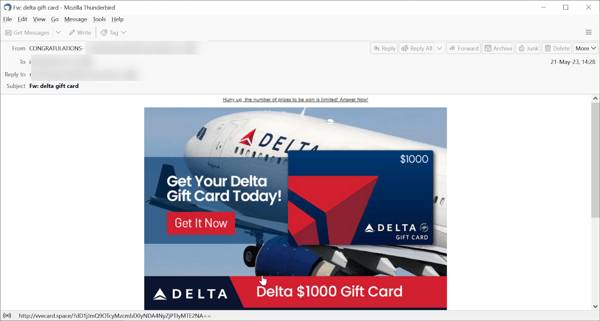
Source: Avanan
Neither the URL or the image takes the recipient to the Delta website.
This use of imagery is nothing new, and there are other examples of actual “pictures in pictures” that are used on websites to confuse visitors into thinking a window needs to be expanded or closed in an effort to get them to click on it, as shown below:
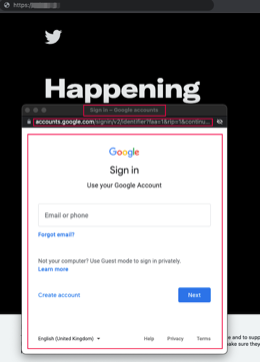
Source: Avanan
It should also be noted that these kinds of emails – along with every other phishing email – are generally too good to be true, or at the very least, are unexpected; something that should raise a red flag for any user that has undergone Security Awareness Training.
Regardless of what Avanan wants to call this type of attack, the reality is that the social engineering value of something as simple as an engaging, branded image is apparently all it takes to get the untrained user to click and fall for the resulting scam.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
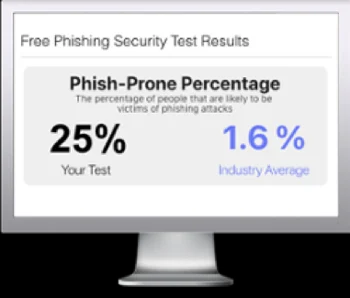
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

