QakBot Banking Trojan Evolves and Now Takes Over Email Conversations to Spread Malware

As if stealing all your credentials, cookies, and email wasn’t bad enough, this new version of QakBot inserts itself into your emails, impersonating you to gain access to more victims.
I’ve covered QakBot before – in fact, just a few months ago where we saw a surge in QakBot’s use jump by 65%. But a new analysis of the most recent version of the banking trojan by security researchers at Sophos details how QakBot has evolved and now wants to spread itself to everyone you know.
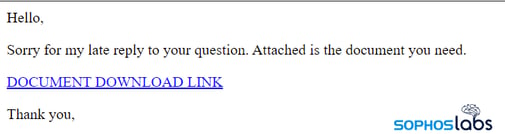
Once infected – generally via phishing attack – QakBot accesses the inbox of the victim user and impersonates the compromised account, sending out phishing emails via a Reply to All of all existing email threads. To make the email look more authentic (and as with all Reply to All emails) the original message being replied to is quoted.
Generally, the malicious email content is little more than a brief business message in the recipient native language and a malicious link.
This type of attack is dangerous for two reasons: first the malicious email spreading QakBot is most definitely coming from someone that the recipient is conversing with already (you). And, second, the email thread is a known conversation. The only thing that makes this attack seem out of place is the abrupt “here – look at this document” that should seem out of place. Those employees that undergo continual Security Awareness Training will see a red flag immediately. But, sadly, those users that aren’t taught to be vigilant will likely click the link and further spread QakBot.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.

Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

