Report: Phishing Remains the Most Prevalent Cyber Threat

INKY has published its annual report on email security, finding that phishing accounted for 30% of all reported cybercrimes last year.
“Phishing threats grew in both volume and sophistication, introducing new attack vectors like QR codes, cross-site scripting, and weaponized file types (e.g., RTF and DOT),” the report says.
“Cybercriminals also increasingly exploited trusted services such as DocuSign and PayPal, underscoring the urgent need for adaptive, robust security solutions.”
Threat actors continue to use QR codes as an alternative to text-based phishing links. Interestingly, as email security solutions have adapted to check for images containing malicious QR codes, attackers have begun using Unicode characters to manually construct QR codes from black and white squares. A phone’s camera will still recognize this as a QR code, but an email filter will simply see a table of text characters.
The researchers also observed an increase in phishing attacks that used URL encoding to conceal malicious links.
“URL encoding converts characters into a format that can be transmitted over the Internet,” INKY explains. “This encoding replaces unsafe ASCII characters with a ‘%’ followed by two hexadecimal digits. Spaces are replaced by ‘+’, and special characters like ‘<’, ‘>’, ‘/’, and others are replaced by their respective hexadecimal codes. Then, to the delight of cybercriminals everywhere, web browsers will automatically decode the obfuscated strings back into ASCII.”
Additionally, attackers are abusing legitimate notifications from services such as Adobe to insert phishing messages.
“Looking for the tell-tale signs of a phishing email is something many of us have come to do automatically,” the report says. “However, things get much trickier when the phishing emails come in the form of legitimate Adobe notifications, have been authenticated (SPF & DMARC) by adobe.com, and use actual Constant Contact tools.”
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
INKY has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
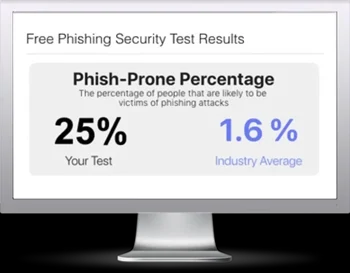
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

