Spear Phishing Attacks Increase 127% as Use of Impersonation Skyrockets

Impersonation of users, domains, and brands is on the rise, as is the use of malicious links, in response to security vendors improving their ability to detect malicious attachments.
I talk often about the back-and-forth that exists between cybercriminal groups and security vendors. Security solutions improve their detection capabilities, and threat actors work tirelessly to find new ways to evade detection. New data found in GreatHorn’s 2023 State of Email Security report shows that this is exactly what’s been happening in the last 12 months. Let me paint the picture for you – according to the report, in 2022:
- Microsoft and Google have improved their attachment scanning capabilities
- Spear phishing increases 127% to focus specific scam themes on specific targets
- Executive Impersonation jumps 344% making the attack seemingly come from a trusted source
- 43% of all potentially dangerous emails are now impersonation emails
- All of the top 20 malicious links used were from compromised domains with positive reputation scores to bypass native scanning controls, such as those used by various Google services
In essence, the cybercriminals now realize they can’t really use malicious attachments, so they’re realizing they need to find a balance between great social engineering against targeted victims, use of impersonation, and the use of legitimate sites to host the malicious payload to achieve this next evolution of attacks.
According to GreatHorn, most attacks take between 1 and 4 steps to get the victim user to interact with the malicious payload.
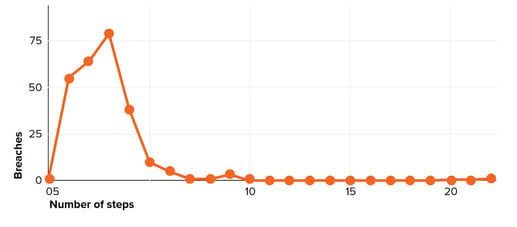
Source: GreatHorn
This means you have a bunch of users that unwittingly follow a set of unusual and unnecessary clicks that they should know better than to follow – something they learn very quickly if they are enrolled in new school Security Awareness Training. Attackers will continue to evolve their craft, so your users need to stay up-to-date on the latest attacks.
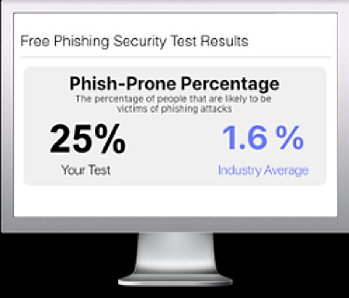
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

