Spear Phishing Campaign Targets Former Israeli Officials

An Iranian threat actor is conducting a spear phishing operation against Israeli officials, according to researchers at Check Point. The targets have included the former Foreign Minister and Deputy Prime Minister of Israel, a former Major General of the Israeli Defense Forces, and a former US Ambassador to Israel.
“One of the straightforward purposes of this campaign is to gain access to the inboxes of its victims, specifically for Yahoo inboxes from the flows we observed,” the researchers write. “The phishing pages include several stages- asking the user for their account ID followed by an SMS code verification page. It is interesting to note that the truncated phone number within the phishing page was customized specifically for the target, and it corresponds to the public records. We suspect that once the victim enters his account ID, the phishing backend server would send a password recovery request to Yahoo, and the 2FA code would allow the attackers to gain access to the victim’s inbox.”
Check Point notes that the attackers used an identity service to add legitimacy to their phishing sites.
“Using a legitimate service to facilitate an attack is always a great bonus for a threat actor,” the researchers write. “It saves resources and the need to develop anything on their own, not to mention that the target and any security solution would be less suspecting of a legitimate service. In this case, the attackers used validation.com, an identity verification service created by the domain registration giant NameCheap, that allows anyone to easily validate their customer’s identity by providing an option to scan an ID or documents directly from the webcam, or by uploading a file…. In this campaign, we have seen one redirection flow from Litby[.]us which leads to a URL on validation.com, and as part of our analysis, we had an indication that the attacker obtained the Passport scan of another high end target. This scan was likely collected by the same means, highlighting the effectiveness of this technique.”
New-school security awareness training can enable your employees to thwart targeted social engineering attacks.
Check Point has the story.
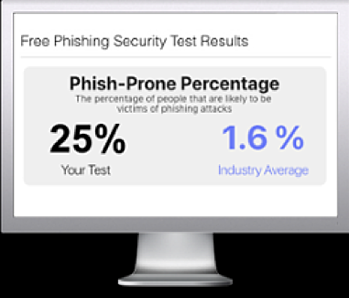
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

