The $44 Billion Smishing Problem and How to Not Be a Victim

Consumer Affairs reported on how big of a problem SMS phishing scams have become, and how it’s about to get a lot worse. According to a recent FBI report, more than 320,000 Americans were targeted by these schemes in 2021, resulting in $44 billion in losses. Consumers on average get an average of 19.5 spam texts per month, over double the rate it was three years ago.
These scams often start with a message that includes a link so a supposed survey, prize winnings, or an urgent notification about a bank account or credit card. Victims are then asked to either go to a website, call a phone number, or enter information that is all controlled by the attackers.
Who Is Being Targeted?
In a nutshell, nobody is immune. Scammers target organizations of all types and sizes, as well as their employees. Ian Matthews, President and CEO of WMC Global, says there’s a simple reason these types of scams are on the rise. “Ninety-seven percent of Americans own some form of a smartphone, with over a quarter of younger Americans and those with income under $30K relying on smartphones for online access.”
One of the favorite tactics used by cybercriminals is finding the names of company employees, and sending a message while pretending to be a fellow employee. Another popular scheme involves using a domain name that only looks legitimate. Smishers know that mobile browsers often don’t display the full URL of a link, so they’ll create one that has just enough of the primary domain name in it to trick their victims into thinking that the link can be trusted.
SIM Swapping
SIM Swapping – the act of transferring a mobile phones’ actual SIM card to one controlled by threat actors – has been around for a number of years. Hackers gather publicly available information about their victims, and use it to contact their target’s mobile carriers and pretend to be them. They claim they need to move their phone number or they lost a device. If the carrier believes them, they will transfer the information from the victim’s SIM card to the one controlled by the attacker.
If the attacker is successful, they can now use the SIM in a phone in their possession to get all their victims’ calls and texts, including any two-factor authentication texts and one-time PINs used for security. With that information, the attacker can now access the victim’s various social media and financial accounts.
This is likely the next big mobile threat. Recently, the FBI warned that SIM swapping attacks had over a 500% increase in the number of attacks and monetary losses.
How Not To Fall Victim
Industry experts agree on the age-old advice, if something is too good to be true, it probably is. That said, here are some common signs to watch out for when receiving an unexpected text:
- Misspellings and grammar mistakes
- Unexpected prizes, gift cards, or even loans
- Anyone asking to confirm sensitive information. The government will never ask you to do this on unsecure channels!
- Be careful with links in SMS messages, just like you would in emails. When in doubt go directly to the website yourself rather than clicking a link
- If something just doesn’t feel right, do not engage with the SMS
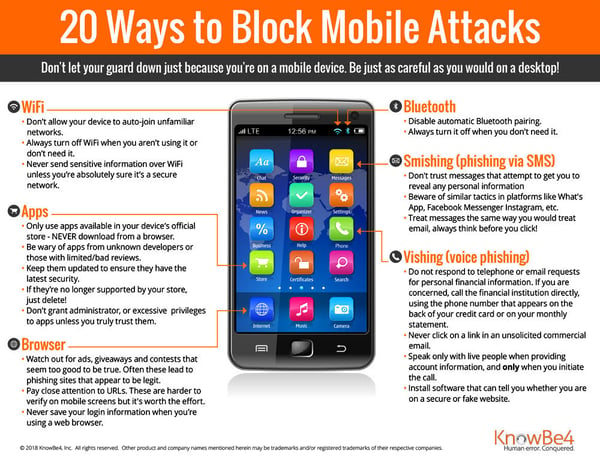
In addition to the above, see our infographic on 20 ways to block mobile attacks:
New-school security awareness training can teach your employees to recognize social engineering attacks.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
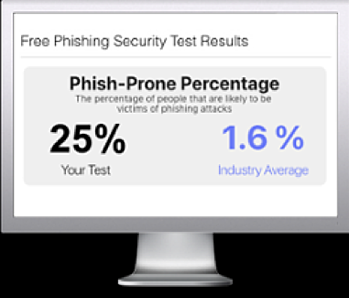
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

