Upgraded Phishing-as-a-Service Platform Drives a Wave of Smishing Attacks

A phishing-as-a-service (PhaaS) platform dubbed ‘Lucid’ is driving a surge in SMS phishing (smishing) attacks, according to researchers at Prodaft.
The platform is operated by Chinese cybercriminals who offer access to the service under a subscription model. A Lucid subscription allows crooks to easily craft sophisticated, targeted phishing campaigns.
“Utilizing various landing and verification pages within Lucid, the panel automatically generates a domain when a domain name is provided, creating an interface tailored to the selected phishing template,” Prodaft explains.
“When creating a template, PhAAS users can customize landing pages for their targeted domains, such as phishingdomain[.]com/xxx. Additionally, the panel allows for dynamic adjustments based on the victim’s IP address, enabling location-based targeting, device-specific focus (iOS or Android), and additional verification steps for users.”
Notably, the kit uses Apple iMessage and Android’s RCS standard, which helps the messages bypass SMS spam filters. These messages also appear more trustworthy to users.
“Sophisticated threat actors leverage psychological factors like visual trust indicators,” the researchers write. “Blue bubbles (iMessage) or ‘Chat message’ indicators (RCS) create a perception of legitimacy compared to green SMS bubbles. Users implicitly trust messages appearing to come through Apple/Google infrastructure.”
The phishing kit’s templates can impersonate “postal services, courier companies, road toll systems, and tax refund agencies” across 88 countries around the world.
“Analysis of targeted organizations, registered domains, and linked phishing panels indicates that a significant number of recent attacks have been coordinated through Lucid PhAAS infrastructure,” Prodaft says. “By pivoting on attack domains, it was determined that 129 distinct Lucid instances deployed within a single month.
Operational data indicates that Lucid-driven campaigns exhibit an average success rate of approximately 5%, with certain domains receiving more than 550 visits per week. In one observed case, a single phishing site recorded 30 compromised credit card details from an equivalent number of victim interactions within a 7-day period.”
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 70,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
BleepingComputer has the story.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
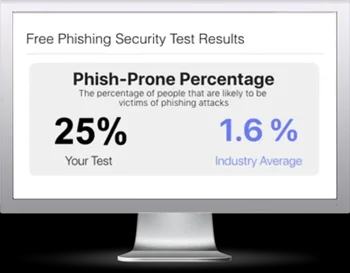
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

