Affinity Phishing Attacks Use Social Engineering Tactics to Prey on Victims

Affinity phishing scams are ones in which criminals cultivate trust in their prospective victims by trading on common background, either real or feigned. Thus a fraudster might claim a common religion, a shared military background, membership in a profession, or a common ethnicity, all with the goal convincing the victim that they can be trusted. What follows all too often one can readily imagine.
The typical affinity scam is one in which the hood pretends to be a nice person, someone the victim can and should trust. But affinity scams can also exploit common fears as much as common affections. That’s what taking place right now with Chinese-Americans who retain close ties to the old country.
“The FBI warns of criminal actors posing as Chinese law enforcement officials or prosecutors in financial fraud schemes targeting the US-based Chinese community. Criminals tell victims they are suspects in financial crimes and threaten them with arrest or violence if they do not pay the criminals.”
Well-known efforts by the Chinese government to pursue immigrants and expatriates living in North America lend specious credibility to this criminal scam. “Criminals exploit widely publicized efforts by the People’s Republic of China government to harass and facilitate repatriation of individuals living in the United States to build plausibility for their fraud. Criminals typically call victims, sometimes using spoofed numbers to appear as if the call is from the Chinese Ministry of Public Security, one of its localized Public Security Bureaus, or a US-based Chinese Consulate. Criminals may also communicate through online applications.”
The criminals will often deploy phony but official-looking documents to press their case. “Criminals may show victims fraudulent documents as proof of these accusations, including realistic-looking arrest warrants or intricate details about alleged criminal schemes. Criminals may also display basic knowledge of the victim to appear more legitimate.”
This is the sort of social engineering against which new school security awareness training can effectively prevent. It can also put their mind to ease.
The FBI’s IC3 has the story.
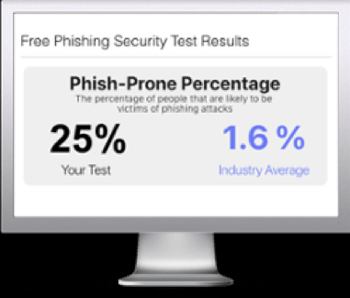
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

