‘Support’ Tops the List of Combosquatted Domains Used in Phishing Attacks

A method used in domain impersonation attacks, combosquatting aids the threat actor by using a modified domain name to further increase the credibility of an attack.
If you aren’t familiar with the term combosquatting, it’s where a threat actor takes a legitimate domain – let’s use companyco.tld and combine another phrase with the domain name to create something like support-companyco.tld. The use of additional words help establish context for a phishing scam or simply are benign enough to be ignored by recipients, according to a new keyword analysis of domain names by threat researchers at Akamai.
The goal is, should the recipient glance at the domain name, it appears to jibe with the phishing campaign’s theming. So, if it’s an attack purporting to be Paypal, using a domain like wwwpaypal-com.[info] with a cursory glance by a non-vigilant user may actually pass muster.
According to Akamai, the use of the term support is most often used – likely as the foundation of an attack aimed at either obtaining credentials or credit card details by convincing the victim that there’s a problem with their account on whatever website the scam is pretending to be from.
This technique is the very reason users need to undergo continual Security Awareness Training. Without it, they will give the sender domain only a cursory glance (and assume it’s legitimate despite how awful the domain name looks), or completely skip checking the sender domain altogether and take them at their word.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
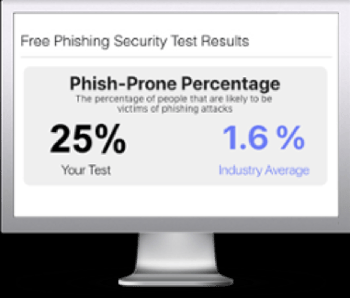
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

