Fake copyright infringement emails install LockBit ransomware

LockBit ransomware affiliates are using an interesting trick to get people into infecting their devices by disguising their malware as copyright claims.
The recipients of these emails are warned about a copyright violation, allegedly having used media files without the creator’s license. These emails demand that the recipient remove the infringing content from their websites, or they will face legal action.
The emails, spotted by analysts at AhnLab, Korea, do not determine which files were unfairly used in the body and instead tell the recipient to download and open the attached file to see the infringement content.
The attachment is a password-protected ZIP archive containing a compressed file, which in turn has an executable disguised as a PDF document, but in reality, is an NSIS installer.
The reason for this wrapping and password protection is to evade detection from email security tools.
If the victim opens the supposed “PDF” to learn what images are being used illegally, the malware will load and encrypt the device with the LockBit 2.0 ransomware.
Copyright claims and malware
While the use of copyright violation claims is interesting, it’s neither novel nor exclusive to LockBit members, as many malware distribution campaigns use the same lure.
BleepingComputer has recently received numerous emails of this sort, which upon further analysis, we discovered were distributing BazarLoader or the Bumblebee malware loader.
.png)
Source: BleepingComputer
Bumblebee is used for delivering second-stage payloads, including ransomware, so opening one of those files on your computer may lead to rapid and catastrophic attacks.
Copyright claims are a matter that publishers of content should take into serious consideration, but if the claim isn’t straightforward but instead requests you to open attached files to view the violation details, it’s improbable for it to be a genuine takedown notice.
LockBit at the top
According to NCC Group’s “Threat Pulse” report for May 2022, published today, LockBit 2.0 accounted for 40% of all (236) ransomware attacks reported in the month.

The notorious ransomware operation recorded a whopping 95 victims in May alone, whereas Conti, BlackBasta, Hive, and BlackCat collectively had 65.
This continues the trend seen by Intel 471, which put LockBit 2.0 at the top of the most prolific ransomware operations in Q4 2021, and further cement the group as one of the most widespread threats.
Belleping Computer has the full story here: https://www.bleepingcomputer.com/news/security/fake-copyright-infringement-emails-install-lockbit-ransomware/
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
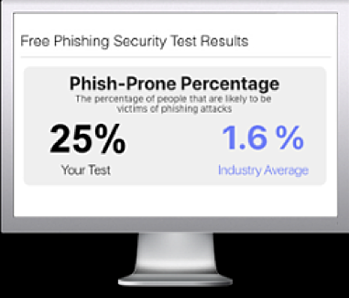
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

