Large-Scale StrelaStealer Campaign Impacts Over 100 Organizations Within the E.U. and U.S.

A new campaign of StrelaStealer attacks identified by security analysts at Unit42 has been spotted targeting E.U. and U.S. organizations. This somewhat new infostealer has evolved to be even better at evading detection in a new string of campaigns aimed at stealing email credentials from well-known email clients.
Credentials are the new currency; get access to someone’s social media or email account and a threat actor has a foothold from which to launch a string of future attacks all impersonating the victim.
Historically, most of the attack numbers on a daily basis have been in the single digits, but last November the first spike of attacks reached nearly 250 in a single day… and then back to single digits.
But then for a little over a week at the end of January and into February, there was another spike:
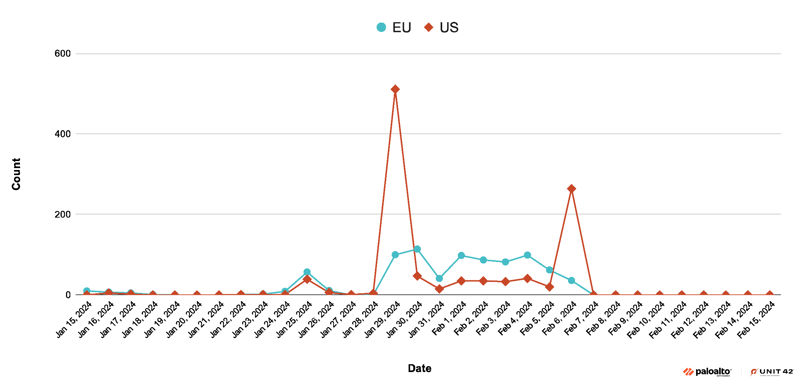
Source: Palo Alto Networks
This latest spike hosted a new variant of the infostealer, with a new packer, obfuscation methods, and more – potentially indicating that this may be a test of the threat groups latest wares before unleashing an even larger-scale attack.
The good news is that the attackers aren’t very good at social engineering; according to Unit42, the emails they employ clearing have a zip file attachment:
Source: Palo Alto Networks
But that doesn’t mean they can’t improve both their writing skills (especially with the help of generative AI) and their use of links, legitimate web apps, and more to create a far more convincing email – something that requires users to enroll in security awareness training to learn to spot and avoid.
KnowBe4 empowers your workforce to make smarter security decisions every day. Over 65,000 organizations worldwide trust the KnowBe4 platform to strengthen their security culture and reduce human risk.
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

