Less Than One-Third of Organizations Leverage Multiple Authentication Factors to Secure Their Environment

Demonstrating a complete lack of focus on the need for additional authentication factors, surprising new data highlights a material security gap that enables cybercrime.
We’ve previously covered industry data that points to the overwhelming majority of cyberattacks use valid accounts (which puts harvesting credentials as a primary attack focus). But new data from MFA hardware vendor Yubico in their State of Global Enterprise Authentication Survey puts a clear focus on the problem – organizations just aren’t implementing multi-factor authentication.
According to the report, a third or less use some form of additional authentication factor:
- 33% use Mobile/SMS pushes
- 30% use a Password Manager
- 29% use a mobile push authentication app
- 20% use hardware keys
What’s more shocking is that 59% of employees rely on simple username and password combinations to authenticate.
This isn’t good folks.
All it takes is one really good social engineering phishing attack and threat actors will have one or more sets of your employee’s credentials. And with no additional authentication factors, cybercriminals have the keys to whatever corporate kingdom the compromised employee has access to.
So, first off, implement MFA. Across the board for everyone. No exceptions.
Second, implement Security Awareness Training – again, across the board for everyone, so that every user is educated on the state of phishing and social engineering attacks, and can help avoid providing threat actors with usernames and passwords (remember, even those orgs with MFA in place are being attacked with MFA Fatigue attacks – making it necessary to train everyone, regardless of MFA status).
Free Ransomware Simulator Tool
Threat actors are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 22 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
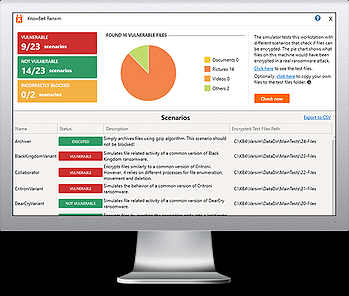
Here’s how it works:
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 23 types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/ransomware-simulator-tool-partner?partnerid=001a000001lWEoJAAW

