Report: 80% of Phishing Attacks Leverage Legitimate Web Infrastructure and Services

Threat actors are taking advantage of every free tool and service they can to improve their chances of successfully fooling security solutions, with compromised websites taking the lead.
New data from Agari and PhishLabs in their just-released Quarterly Threat Trends & Intelligence report shows that those behind phishing attacks are relying on web services, tools, and hosting that would not be initially interpreted as being malicious in four out of 5 attacks. This has huge implications on security software designed to “follow” links within emails to establish that they aren’t malicious in nature.
According to the report, just under 83% of all technology, tools, etc. used by phishing attacks uses legitimate sites and services – of which nearly 42% represents compromised websites.
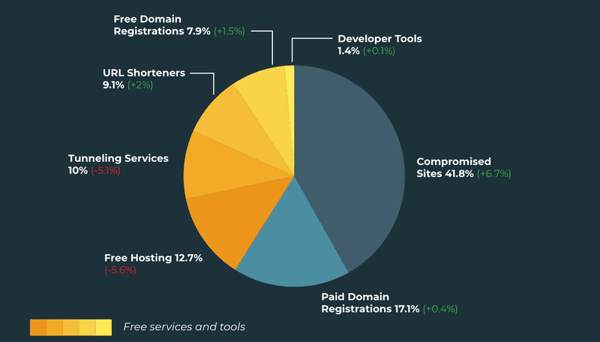
Source: Agari and PhishLabs
Also notable in the image above is the growth in the usage of compromised sites, free domain registrations, and URL shorteners – all indicators of tactics we will continue to see used to avoid detection.
These specific tactics also mean an increase in the use of social engineering, something only defeated by continual Security Awareness Training designed to educate users on what to look for when interacting with email. It’s evident that a portion of phishing emails will get through to the Inbox by using the above tactics; so be sure your users play a role in spotting and stopping phishing attacks by teaching them what a phishing attack looks like.
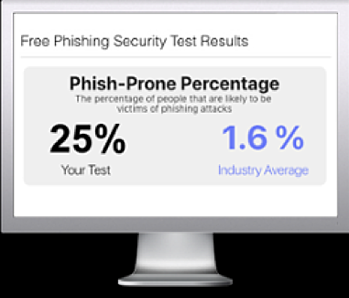
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

