Smishing Campaign Expands to the Middle East

A Chinese-speaking phishing gang has expanded its targeting from the Asia-Pacific region to the Middle East, researchers at Group-IB have found. The gang, which the researchers call “PostalFurious,” impersonated a toll operator and a postal service in the Middle East.
“In the aforementioned fake toll payment scheme, local residents receive fake messages asking them to urgently pay a vehicle trip fee to avoid additional fines,” the researchers write. “The text messages contain a shortened URL to obscure the true phishing address. Once a user clicks on the link, they are redirected to a fake branded payment page. The scammers’ goal is to compromise users’ payment data. Upon closer examination of the phishing infrastructure, Group-IB investigators found an almost identical scam campaign launched on April 29, 2023. The scammers used the same servers to host another network of phishing websites. The only difference between the two scam campaigns, which commenced two weeks apart, is the impersonated brand. In the latter campaign, scammers mimicked a Middle Eastern postal operator.”
10The scammers are sending SMS messages with phony package delivery notifications.
“The latest scam wave also relies on smishing (SMS phishing) to deliver phishing links,” the researchers write. “The text messages were sent from phone numbers registered in Malaysia and Thailand, as well as via email addresses through iMessage. While it is unknown how many individuals were targeted in this campaign, Group-IB experts found that customers of multiple Middle Eastern telecommunications companies received rogue SMS messages. The URLs from the texts lead to fake branded payment pages that ask for personal details, such as name, address, and credit card information. The phishing pages appropriate the official name and logo of the impersonated postal service provider.”
Anna Yurtaeva, Senior Cyber Investigation Specialist at Group-IB’s Digital Crime Resistance Center in Dubai, stated, “Phishers are becoming more prolific and elaborate. They can no longer be detected and stopped by automated blocking. People should stay vigilant and aware of ongoing scams. PostalFurious operations demonstrate the transnational nature of organized cybercrime and emphasize the need for a coordinated joint response that involves the general public, private sector, and government.”
New-school security awareness training can give your organization an essential layer of defense by enabling your employees to recognize social engineering attacks.
Group-IB has the story.
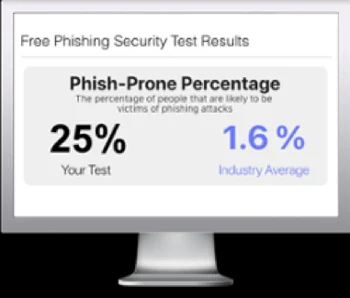
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

