Verizon: Email Reigns Supreme as Initial Attack Vector for Ransomware Attacks

My analysis of this year’s newly-released Verizon Data Breach Investigations Report begins with ransomware findings that point back to users as a big problem.
If you only read one report each year to give you an idea of what’s going on with cyber attacks, it’s Verizon’s Data Breach Investigations Report (DBIR). Each year, analysts sort through tens of thousands of data breach incidents (some successful, some not) and identify the attack patterns.
This year, I wanted to start with some findings on ransomware – but let me back up just a bit with some DBIR data that brings us to ransomware. According to the report, 24% of data breaches include ransomware (putting this type of attack as the number 3 action variety across all breaches) – keep in mind this is a data breach report, so any kind of data breach (including, say, losing a laptop, is included in this report). But according to the report, the second most common attack pattern in all incidents (read: attacks that do and do not include documented data breaches) was System Intrusion (just behind denial-of-service attacks). Within system intrusion attacks, ransomware was involved in over 80% of attacks.
And now that we’re zeroed in on ransomware, we find that email is the number one attack vector.
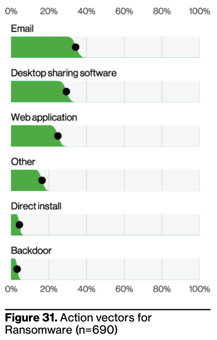
Source: Verizon
This shouldn’t come as a surprise; the DBIR has ransomware as 74% of breaches involve a “human element,” which Verizon defines as “Error, Privilege Misuse, Use of stolen credentials or Social Engineering.”
Tying email back in as the primary attack vector, we can see that social engineering and the stealing of credentials tie in nicely here. These attacks are all leading us back to a user that falls for phishing emails, clicks links or opens attachments, and unwittingly gives up their credentials to threat actors for use in a subsequent attack.
This is why I’m so passionate about the need for Security Awareness Training – it’s the one security measure that addresses the human element Verizon talks about. Through continual education, users can work with a security culture mindset, reducing the risk of falling for social engineering attacks – whether they come in the form of an email, text, phone call, social media, or the web.
Free Ransomware Simulator Tool
Threat actors are constantly coming out with new strains to evade detection. Is your network effective in blocking all of them when employees fall for social engineering attacks?
KnowBe4’s “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 22 ransomware infection scenarios and 1 cryptomining infection scenario and show you if a workstation is vulnerable.
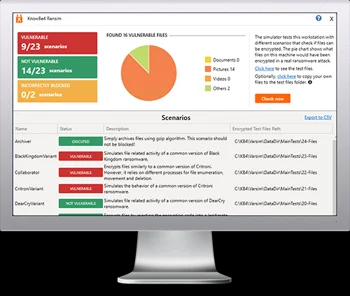
Here’s how it works:
- 100% harmless simulation of real ransomware and cryptomining infections
- Does not use any of your own files
- Tests 23 types of infection scenarios
- Just download the install and run it
- Results in a few minutes!
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/ransomware-simulator-tool-partner?partnerid=001a000001lWEoJAAW

