Than Half of all Email-Based Cyberattacks Bypass Legacy Security Filters

New data shows that changes in cybercriminals’ phishing techniques are improving their game, making it easier to make their way into a potential victim user’s inbox.
I recently wrote about how 12% of all email threats were getting all the way to the inbox. But new data from cybersecurity vendor Armorblox’s 2023 Email Security Threat Report shows that the number is much higher, depending on the security solutions in place.
Of all phishing attacks that targeted organizations in 2022, 78% used sophisticated techniques to successfully bypass native email security tools – and were able to reach the inbox 56% of the time!
According to the report, the following is the breakdown of the kinds of specific attacks and threats found within the phishing attacks:
- 51% of email attacks focused on credential phishing
- 41% focused on social engineering-based threats
- 3% were VIP impersonation attacks
- 3% were extortion attacks
- 2% were payroll fraud scams
By looking at the breakdown of the two largest techniques used, you can begin to see reasons why these attacks are getting through. Credential phishing attacks are successful because they are using new sophisticated ways to avoid detection. Social engineering attacks most often have no malicious content within them, making it difficult to detect.
The risk of such attacks succeeding is high, making it necessary for you to enroll users into continual Security Awareness Training to educate them on what to look for, the techniques used, and how to spot a malicious email a mile away.
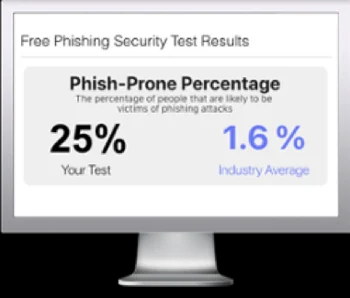
Free Phishing Security Test
Would your users fall for convincing phishing attacks? Take the first step now and find out before bad actors do. Plus, see how you stack up against your peers with phishing Industry Benchmarks. The Phish-prone percentage is usually higher than you expect and is great ammo to get budget.
Here’s how it works:
- Immediately start your test for up to 100 users (no need to talk to anyone)
- Select from 20+ languages and customize the phishing test template based on your environment
- Choose the landing page your users see after they click
- Show users which red flags they missed, or a 404 page
- Get a PDF emailed to you in 24 hours with your Phish-prone % and charts to share with management
- See how your organization compares to others in your industry
PS: Don’t like to click on redirected buttons? Cut & Paste this link in your browser: https://info.knowbe4.com/phishing-security-test-partner?partnerid=001a000001lWEoJAAW

